
tshark
TShark: Command-Line Packet Analysis for Network Security
TShark puts Wireshark's packet analysis power directly in your terminal, enabling automated security monitoring and forensic investigation.

tshark
TShark puts Wireshark's packet analysis power directly in your terminal, enabling automated security monitoring and forensic investigation.
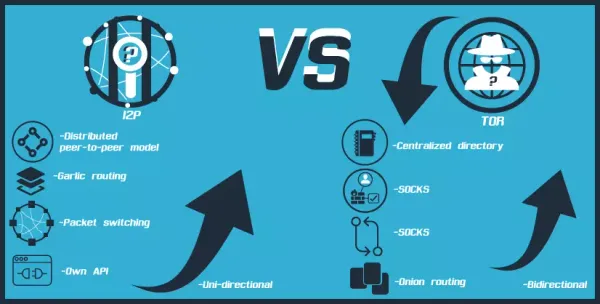
I2P
The Invisible Internet Project (I2P) just announced something remarkable: multiple new, fully-functioning I2P router prototypes have emerged, marking a pivotal moment for privacy-focused networking.
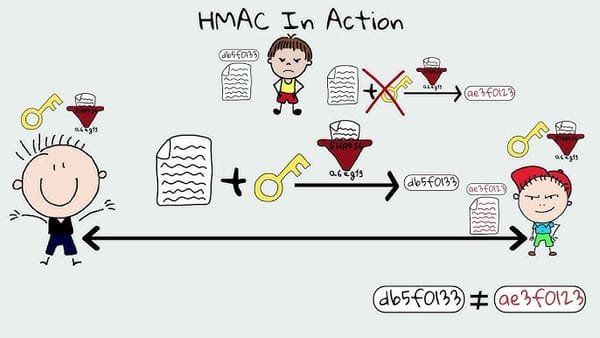
HMAC
RFC 2104 says you need at least 80 bits, but NIST's new SP 800-224 dropped the floor to 32 bits with a risk analysis requirement that nobody wants to explain.

qubes os
The Xen Project dropped three security advisories on September 9, 2025, and Qubes OS published same-day confirmation that none of them threaten the platform's security architecture.

Microsoft
Microsoft wants AI agents clicking through your files like humans—on infrastructure with 1,360 CVEs in 2024 alone.

linux
LMDE 7 "Gigi" released October 14, 2025 built on Debian 13 Trixie with Linux kernel 6.12 LTS, Cinnamon 6.4.12, and the first mainline real-time kernel support.

AI
California just mandated that police must disclose when artificial intelligence writes their reports, and vendors are banned from selling the data they collect. (and why it doesn't matter)

tor project
The privacy OS now opens Tor Browser to a local page instead of phoning home, while patching critical vulnerabilities and fixing confusing error messages.
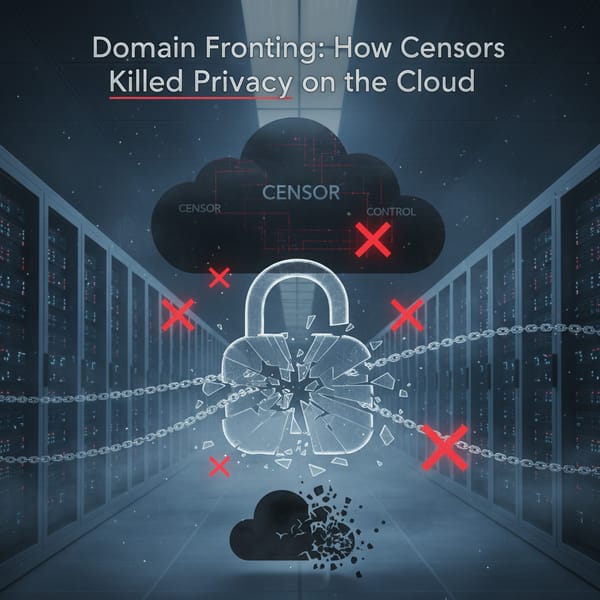
domain fronting
By putting one domain in the TLS handshake and another in the HTTP header, domain fronting made Signal unstoppable in Egypt, Oman, and UAE—until corporations caved to authoritarian pressure.

Cryptpad
While Google Docs reads everything you type, CryptPad's XSalsa20-Poly1305 encryption and Nakamoto-style consensus protocol ensure the server never decrypts your documents.
Monero
The new release implements /24 subnet filtering to disadvantage spy nodes that have been attempting transaction-to-IP correlation since October 2020.

member
Your ISP-provided router might be saving you setup time, but it's costing you control, privacy, and protection against nation-state attackers who've already proven they can breach these devices.