Threat-Models
Building Proper Threat Models: What Most People Get Wrong About OPSEC
Effective threat models assess specific adversary capabilities and attack surfaces rather than implementing random security measures.
Threat-Models
Effective threat models assess specific adversary capabilities and attack surfaces rather than implementing random security measures.
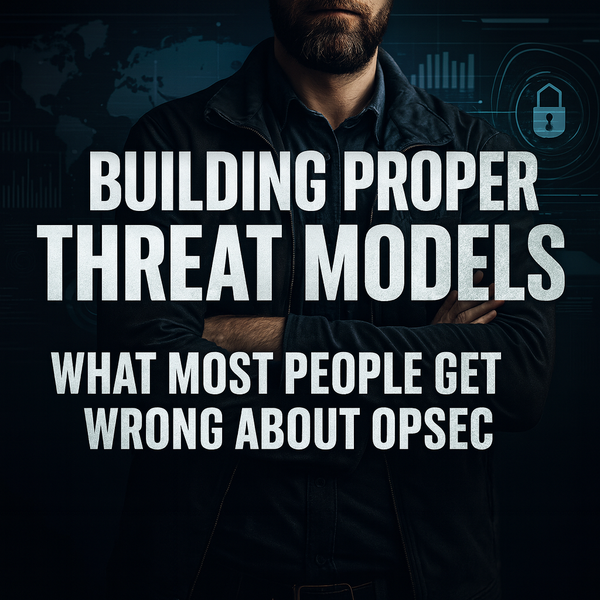
I2P
I2P's garlic routing provides superior anonymity through bidirectional tunnels and distributed architecture without central authorities.
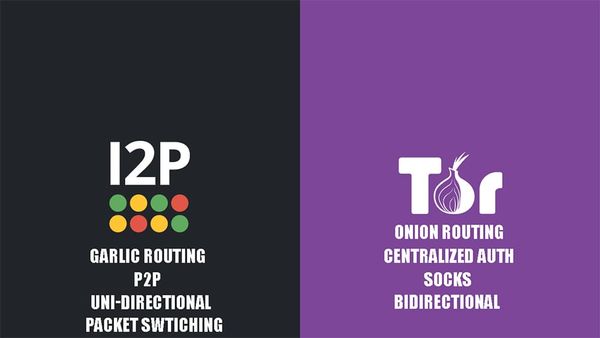
npm malware
The package literally advertised itself as an 'enhanced stealth wallet drainer' in its own source code, and npm still served it up for days.

LibreWolf
LibreWolf strips Firefox of corporate surveillance while implementing aggressive fingerprinting resistance and privacy hardening.

Monero
Monero uses ring signatures, stealth addresses, and RingCT to provide complete transaction privacy through cryptographic mathematics.
samourai
The code they wrote remains free, waiting for the next generation of developers smart enough to never attach their names to it.

darknet vendor
Sydney cops busted Ricky Cao (25) and Henry Do (22) for running a dark web drug syndicate from suburban bedrooms, moving 4kg of cocaine, heroin, ice and ketamine nationwide until a single $630 crypto transaction exposed their operation to five months of surveillance.

Darknet Markets
Tor2onMarket, a leading dark web marketplace with over $15 million in transaction volume, deployed rotating emergency mirror addresses on July 6, 2025, after coming under DDoS attack.

Matrix
The Matrix ecosystem's compliance gambit might actually matter
indicted
Seven Georgia residents now face federal conspiracy charges after allegedly operating a high-volume fentanyl and methamphetamine distribution network through dark web markets.

opsec
Dread's /d/opsec is rotting and infected cut. Today we talk about Nihilist's alternate platform, where you can get paid in Monero for QUALITY submissions.

X11
Major Linux distributions are systematically destroying three decades of user freedom by forcibly removing X11 support, abandoning accessibility tools that blind users depend on, and eliminating 32-bit compatibility—all while corporate sponsors like IBM-owned Red Hat pull the strings.