Whonix 18 Testing Rewrites Kloak for Wayland Protection
The Tor anonymity OS enters testing with a keystroke anonymization rewrite featuring native Wayland support and IPv6 across the network stack.

Your typing patterns can create a behavioral fingerprint that persists across sessions, devices, and anonymity tools. The time between key presses, the rhythm of common letter combinations, and the duration you hold keys down form a biometric signature that researchers have demonstrated can identify individuals with accuracy rates significant enough for deanonymization. The Whonix 18.0.7.5 testing release, announced November 27, 2025 with upgrade testers wanted, addresses this with a complete rewrite of kloak, the keystroke anonymization tool, now featuring native Wayland support.
The original kloak worked by intercepting keyboard events at the device level and introducing random delays before passing them to applications. This obfuscated the timing information that makes keystroke biometrics work. The problem was architectural: kloak depended on X11, and the security community has been migrating away from X11 to Wayland for years because X11 allows any application to spy on any other application's input and output. Running kloak on X11 protected keystroke timing while leaving users vulnerable to the broader input capture problem that Wayland solves.
The Whonix 18 kloak rewrite operates natively under Wayland, maintaining keystroke timing protection without requiring the compromised X11 security model. The default delay of 100 milliseconds achieves roughly 20-30% reduction in identification accuracy according to the project's self-reported testing. Mouse movement obfuscation received similar attention, though the developers note kloak handles keyboard behavior more effectively than mouse patterns.
Non-Qubes-Whonix includes kloak by default on the Workstation. Qubes users get Qubes Event Buffering instead for R4.3 and above, since the Qubes architecture handles input events differently. Installing kloak on the host system in addition to the Whonix VM provides defense in depth: if the Workstation gets compromised, the host-level kloak still protects typing patterns.
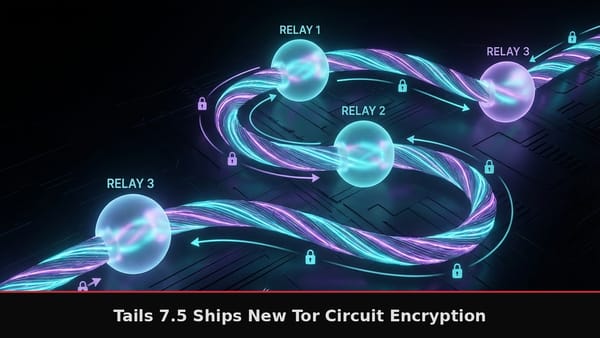
IPv6 support arrives across the network stack. This matters because Tor has been expanding IPv6 support, and the Whonix firewall rules, address assignment logic, and network configuration needed corresponding updates. The dual-stack capability means Whonix can route traffic through IPv6-capable Tor relays when available.
The Whonix architecture isolates all network activity into two virtual machines. The Gateway runs Tor exclusively and handles all network routing. The Workstation has no direct internet connection and knows nothing about the real external IP address. All traffic from Workstation applications passes through the Gateway's Tor processes via an internal virtual network. This design means a compromised Workstation application still cannot bypass Tor because the Workstation literally has no path to the internet except through the Gateway, assuming the virtualization layer remains secure.
Version 18 enables user-sysmaint-split by default on Whonix-Gateway, separating regular user accounts from system maintenance functions for improved privilege isolation. The desktop shifts from Xfce to LXQt with Wayland support, matching the Kicksecure changes since Whonix builds on Kicksecure's hardened Debian base.
Network debugging gets easier with nmap and nping included by default. These tools run through Tor like everything else in Whonix, allowing network diagnostics without compromising anonymity.
Systemd service restructuring optimizes Tor startup sequences. The changes merge related services and improve network initialization ordering, reducing boot time while maintaining the careful sequencing that prevents traffic leaks during startup.
AppArmor integration receives improvements with updated sandboxing profiles. AppArmor restricts what applications can access on the filesystem and network, providing mandatory access control that limits damage from compromised applications.
The Workstation remains unaware of its real external IP address by design. Over a decade of testing with corridor (a Tor traffic whitelisting gateway) and other leak tests has not discovered IP leak vulnerabilities in tested scenarios. The iptables-based firewall on the Gateway blocks any traffic that would bypass Tor, making it architecturally impossible for applications to leak the real IP even with root privileges on the Workstation.
Download options include VirtualBox OVA files and KVM/libvirt images. Qubes integration follows a separate announcement. In-place upgrades from Whonix 17 to 18 use documented release upgrade procedures.
Known keyboard layout issues require restarting kloak with Right Shift + Escape after changing layouts for the new configuration to take effect. This matches the same issue in Kicksecure 18 since both distributions share the labwc Wayland compositor configuration.