TShark: Command-Line Packet Analysis for Network Security
TShark puts Wireshark's packet analysis power directly in your terminal, enabling automated security monitoring and forensic investigation.

TShark puts Wireshark's packet analysis power directly in your terminal, enabling automated security monitoring and forensic investigation.


Dread is running a writing contest with $1,750 in Monero prizes and one very specific ban: AI-generated content.
Apple rolled identity verification into iOS 26.4 for UK users under the Online Safety Act, requiring credit card scans or government photo ID to confirm users are over 18. If you decline, app downloads and in-app purchases get restricted on a phone you already own. The system is expanding
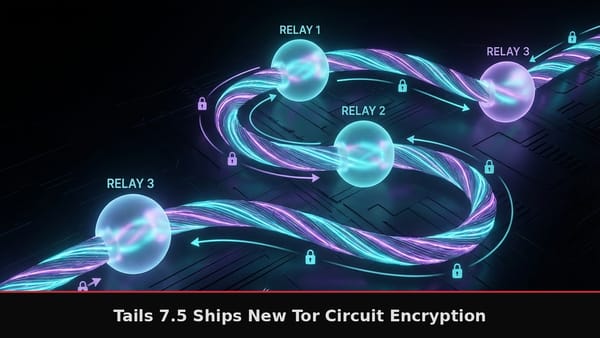
Tails 7.5 upgrades to Tor 0.4.9.5 with Counter Galois Onion encryption and patches over 30 high-severity Firefox vulnerabilities through Tor Browser 15.0.7.

On February 3, 2026, the I2P anonymity network was flooded with 700,000 hostile nodes in what became one of the most devastating Sybil attacks an anonymity network has ever experienced. The network normally operates with 15,000 to 20,000 active devices. The attackers overwhelmed it by a factor