Tor Onion v3 Services: Descriptor Rotation and Scalability
Tor onion v3 services utilize Ed25519 cryptography and sophisticated descriptor rotation protocols to achieve enhanced security and scalability for anonymous hidden service operations.
Tor onion v3 services revolutionize anonymous communication through improved cryptographic foundations that replace RSA-1024 with Ed25519 signatures while implementing sophisticated descriptor rotation protocols that enhance both security and scalability for hidden service operations. Tor onion v3 specification demonstrates how v3 services achieve 56-character onion addresses through elliptic curve cryptography that provides equivalent security to 3072-bit RSA while enabling efficient signature verification and key management across the distributed Tor network infrastructure.
Tor Onion v3 Services
1. Cryptographic Evolution
Tor onion v3 replaces RSA-1024 with Ed25519 signatures, delivering stronger security and faster verification.
- RSA-1024 ≈ 80-bit security
- Ed25519 ≈ 128-bit security
- Equivalent to RSA-3072 in strength
Ed25519 provides stronger protection than RSA-1024
2. 56-Character Onion Addresses
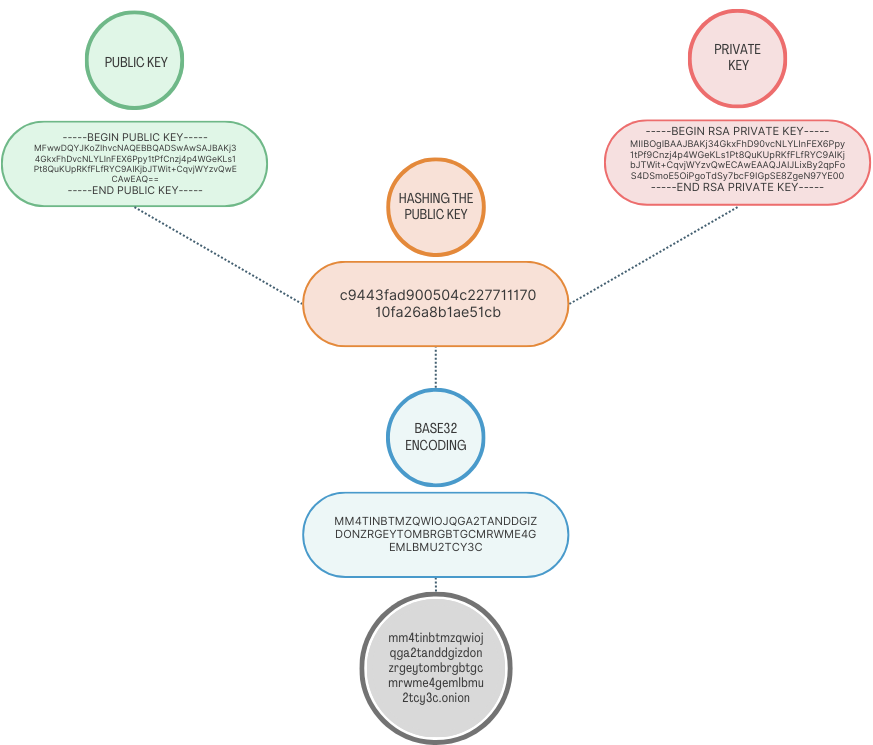
v3 services create 56-character addresses using deterministic derivation from Ed25519 public keys, embedding cryptographic identity into the address itself.
pubkey → checksum → base32 → 56-char .onion
Example: myst3xampl3addresstestexampleexampleexampleexampleexampleexample.onion
3. Descriptor Rotation Protocols
Service descriptors rotate frequently, limiting exposure if a descriptor is compromised and improving scalability across the Tor network.
Descriptors (D1, D2, …) rotate to maintain anonymity & resilience.
4. Distributed Network Security
By combining stronger cryptography, deterministic address generation, and descriptor rotation, Tor v3 enhances:
- Identity security (public key embedded in address)
- Operational scalability (frequent descriptor rotation)
- Performance (faster signature verification)
Cryptographic Foundation and Address Generation
Ed25519 signature scheme provides the mathematical foundation for efficient public key operations with 128-bit security levels through elliptic curve discrete logarithm assumptions. Onion v3 addresses derive from Ed25519 public keys through a deterministic process that includes checksum verification and base32 encoding, creating 56-character addresses that embed cryptographic identity verification directly into the service identifier.
Identity key management utilizes long-term Ed25519 signing keys that establish cryptographic identity for hidden services across multiple sessions and descriptor rotations. The identity key serves as the root of trust for deriving blinded signing keys and descriptor-signing keys while remaining separate from encryption keys used for actual communication, enabling key rotation and forward secrecy without changing service addresses. The identity key itself is encoded in the onion address but does not appear directly in service descriptors.
Forward secrecy implementation generates ephemeral key pairs for each connection session, ensuring that compromise of long-term identity keys cannot decrypt previous communication sessions. Key rotation protocols enable periodic replacement of encryption keys while maintaining service continuity and preserving the cryptographic binding between service addresses and identity verification mechanisms.
Tor v3 implements restricted discovery through a client authorization system. Each authorized client has a unique x25519 public key, which is used to encrypt the service descriptor so that only those clients can decrypt and fetch it. Authentication itself is handled separately: clients present ed25519 keys during the introduction process, while the service descriptor is signed by a descriptor-signing ed25519 key that is certified by a blinded key derived from the long-term identity key. This separation ensures that encryption and signing are handled by the appropriate cryptographic primitives.
These authentication protocols utilize cryptographic credentials rather than certificate-based systems, balancing access control requirements against anonymity preservation and operational security considerations for sensitive hidden services.
Descriptor Publication and Hash Ring Distribution
Hidden service descriptors contain essential routing information including introduction point addresses, descriptor-signing keys, and operational parameters that enable client connection establishment while providing freshness guarantees through time-based rotation schedules. Tor directory protocol documents the descriptor format showing how cryptographic signatures from descriptor-signing keys (certified by blinded signing keys derived from the identity key) bind descriptor content to service identity while enabling verification of authenticity and integrity.
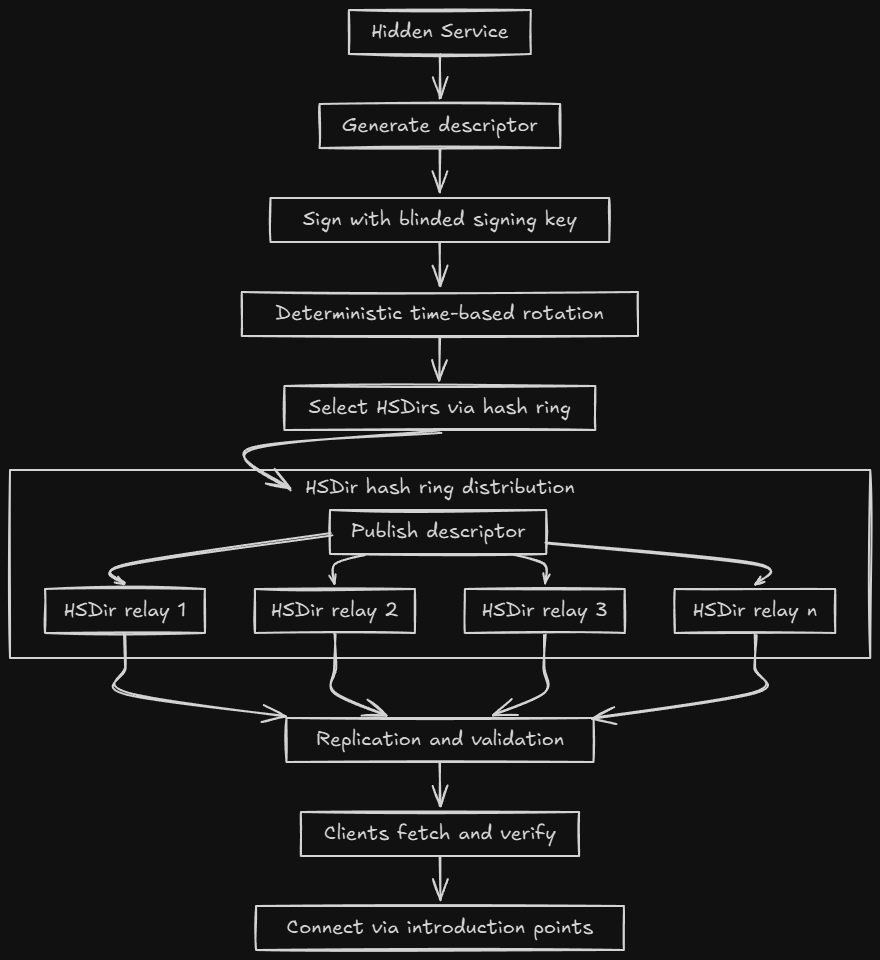
Descriptor rotation timing follows deterministic schedules based on service identity and current time periods to ensure predictable availability while preventing timing correlation attacks that might reveal service operational patterns. Rotation intervals balance freshness requirements against network overhead and descriptor propagation delays that affect service availability during transition periods.
Directory publication relies on a deterministic HSDir hash ring. Hidden service descriptors are mapped to HSDir-flagged relays based on the service’s blinded key and the current time period. Directory authorities assign the HSDir flag to eligible relays, but they do not directly choose which relays host a given descriptor. Instead, the algorithm selects them automatically, uploading two replicas to four HSDirs each by default. This ensures redundancy, availability, and resilience without relying on a central point of control.
Fault tolerance mechanisms include descriptor replication across multiple HSDir relays, validation procedures that detect corrupted or malicious descriptors, and recovery protocols that enable continued service operation despite directory server failures or network partitions. Redundancy strategies ensure service availability even when significant portions of directory infrastructure become unavailable.
Service Discovery and Connection Establishment
Client-side descriptor fetching involves querying multiple HSDir relays to retrieve current service descriptors while implementing validation procedures that verify cryptographic signatures from descriptor-signing keys and descriptor freshness. Discovery protocols include retry mechanisms, fallback strategies, and error handling that ensure robust service access despite network disruptions or directory server unavailability.
Client-Side Descriptor Fetching HSDir
- Query multiple HSDirs → no single point of failure/censorship.
- Verify descriptor signature (descriptor-signing key).
- Enforce freshness (lifetime + revision counters); drop stale.
- Retries + HSDir rotation + error handling for robustness.
Introduction Point Selection Unpredictable
- Constrained randomness → hard to pre-position adversaries.
- Filters: stability flags, bandwidth, uptime (not geography).
- Outcome: capacity + reliability; lowers correlation risk.
Rendezvous Protocol Location-Hiding
- Client picks rendezvous point (RP) + one-time token.
- Client tells service via intro point: meet at RP with token.
- Service connects to RP; RP splices circuits for both sides.
- Forward secrecy; service authenticates to client. Optional: client creds.
Circuit Construction Onion Routing
- Multi-hop path; each relay knows only prev/next.
- Layered encryption → confidentiality + unlinkability.
- Traffic-analysis resistance; hides both endpoints.
- Result: private, authenticated service access.
Introduction point selection algorithms choose relay nodes for service introduction through constrained random selection based on factors including Tor's stability flags, bandwidth capacity, and uptime history while avoiding predictable patterns. Selection strategies prioritize relays meeting Tor's operational requirements rather than geographic distribution, ensuring adequate service capacity and reliability while maintaining resistance to correlation attacks.
Rendezvous protocol coordinates anonymous connection establishment between clients and services through intermediary relay nodes that facilitate communication without revealing network location or identity information. The protocol implements forward secrecy and service authentication to the client while enabling efficient bidirectional communication establishment. By default, the handshake proves the service identity to the client rather than providing mutual authentication, though optional restricted discovery can require client credentials.
Circuit construction utilizes layered encryption and onion routing principles to establish anonymous communication channels that protect both client and service location privacy while providing end-to-end communication security. Anonymous communication protocols demonstrate how layered encryption and relay selection contribute to traffic analysis resistance through the established Tor circuit building process.
Scalability Optimization and Performance Enhancement
High-traffic service deployment requires careful resource management including bandwidth allocation, connection limits, and introduction point scaling that enable reliable service operation under heavy load while maintaining anonymity guarantees. Tor performance optimization techniques balance throughput requirements against security and anonymity preservation for production hidden services.
Load balancing strategies distribute client connections across multiple introduction points and service instances to prevent bottlenecks and ensure acceptable response times during peak usage periods. Balancing algorithms consider factors including relay capacity, network stability, and client diversity to optimize both performance and anonymity properties while respecting Tor's relay selection constraints.
Service distribution enables global service availability through coordinated deployment of service instances across multiple regions while maintaining consistent service identity and synchronized content. Distribution strategies address challenges including content synchronization, failover coordination, and regional network characteristics that affect service performance and availability.
Resource monitoring implements comprehensive tracking of service performance metrics including connection success rates, descriptor availability, circuit establishment latency, and bandwidth utilization that enable proactive optimization and capacity planning. Monitoring systems balance operational visibility against operational security requirements that limit information exposure.
Security Analysis and Operational Considerations
Tor network research provides comprehensive guidance on hidden service deployment best practices including operational security procedures, key management, infrastructure hardening, and monitoring strategies that minimize security risks while enabling reliable service operation. Best practices address both technical implementation details and operational procedures required for secure hidden service deployment.
Traffic analysis resistance utilizes Tor's circuit padding framework and research-based defense mechanisms that provide some protection against network adversaries attempting to correlate client access patterns with service usage. While Tor implements padding protocols and has developed various research defenses, comprehensive traffic analysis resistance remains an active area of development rather than a fully deployed network-wide capability.
Network security analysis examines security considerations specific to hidden service operations including correlation attacks, traffic confirmation, and long-term statistical analysis that could compromise service anonymity. Security analysis informs deployment decisions and operational procedures that minimize exposure to various threat models and adversarial capabilities while acknowledging the current limitations of traffic analysis defenses.
Operational security encompasses physical security, personnel security, communication security, and technical security measures that protect hidden service operations against both network-based and physical threats. Comprehensive security requires careful attention to all aspects of service deployment and operation that could compromise service security or operator anonymity, recognizing that perfect anonymity against all adversaries remains a challenging goal requiring multiple layers of protection.