Proton Helped the FBI Unmask a Protester. Then Said They Didn't.
Proton has handed over user data in response to over 40,000 government orders since 2017. Their own transparency report shows a 94% compliance rate. Here's everything they don't want you to know, sourced from their own documents.


1. The Numbers They Published Themselves (40,389 orders and a 6% fight rate) 2. "Zero-Access" Means Zero Access to Data at Rest, Not Zero Access to Your Emails (their privacy policy vs their marketing) 3. What Proton Can Actually See (it's not a short list)| 4. The IP Logging They Tried to Hide (Wayback Machine receipts) 5. The Phrack Incident: Suspend First, Investigate Never (cluster-banning journalists on a tip) 6. Swiss Privacy: The Brand, Not the Shield (six companies across five countries) 7. Privacy Company Requires You to De-Anonymize Yourself to Sign Up (try Tor and see what happens) 8. Proton Business VPN: The Quiet Admission (the logging infrastructure already exists) 9. The Bitcoin Wallet from the Privacy Company That Wouldn't Accept Monero (they built a wallet for the surveillance coin) 10. $100 Million and a CERN Pedigree (their lobbyist is APCO Worldwide out of DC)|} 11. The Political Neutrality Question (the CEO picked a side) 12. The Affiliate Machine (100% commission and a dedicated influencer contact) 13. HideMyAss: We've Seen This Movie Before (same marketing, same ending) 14. What Privacy Actually Looks Like (what actually works) 15. Sources 16. FAQ: The Counterarguments, Addressed (16 arguments, destroyed)
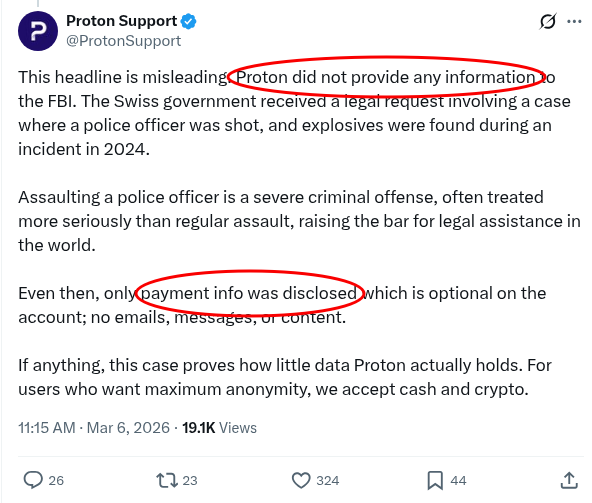
On March 5, 2026, 404 Media published an FBI affidavit404 Media published an FBI affidavit showing that Proton Mail handed over payment data that identified an anonymous Stop Cop City protester in Atlanta. The account, defendtheatlantaforest@protonmail.com, was listed on the Defend the Atlanta Forest Facebook page. The FBI submitted a request through the US-Switzerland Mutual Legal Assistance Treaty. Swiss authorities approved it. Proton provided a credit card payment identifier.
The FBI traced that identifier through the issuing bank to the cardholder. The person was arrested at Atlanta's airport.
The charge was trespassing. The FBI affidavit was authored by a Domestic Terrorism squad special agent. Not a terrorism charge but rather, a trespassing charge, investigated by the domestic terrorism unit, using an international treaty to unmask someone who paid for encrypted email with a credit card.
What's the issue in the picture?
https://x.com/ProtonSupport/status/2029863513695412597?s=20https://x.com/ProtonSupport/status/2029863513695412597?s=20
Credit: @BarbossHack@BarbossHack
Proton's response on X is already a case study in corporate doublespeak. Paragraph one: "Proton did not provide any information to the FBI." Paragraph three of the same post: "only payment info was disclosed."
Edward Shone, Proton's head of communications, tried the same framing with 404 Media: "We want to first clarify that Proton did not provide any information to the FBI, the information was obtained from the Swiss justice department via MLAT." Whether you hand the gun to the guy who pulls the trigger or hand it to a guy who hands it to the guy, the result is the same. The data ended up in the FBI's hands.
The protester got arrested.
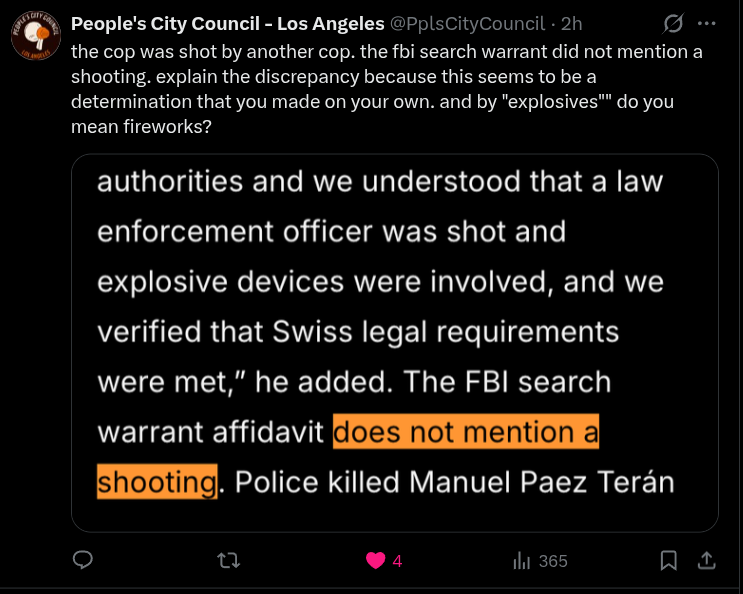
Proton also characterized the case as involving "a police officer was shot, and explosives were found." The FBI's own search warrant affidavit doesn't mention a shooting. @PplsCityCouncil@PplsCityCouncil on X called them out: "the cop was shot by another cop. the fbi search warrant did not mention a shooting. explain the discrepancy because this seems to be a determination that you made on your own. and by 'explosives' do you mean fireworks?"
https://x.com/PplsCityCouncil/status/2030037623297749042?s=20https://x.com/PplsCityCouncil/status/2030037623297749042?s=20
Credit: @PplsCityCouncil@PplsCityCouncil
Proton inflated the severity to justify their compliance. The actual arrest was for trespassing. The person apparently hasn't been charged since.
And Proton processes payments through ChargebeeChargebee, an American company. Your credit card data for your 'Swiss privacy email' goes through a US payment processor.
That's the payment identifier the FBI traced.
Multiple people in the replies immediately pointed out that if this user had paid with Monero, there would have been no payment identifier to trace. Proton's response says "for users who want maximum anonymity, we accept cash and crypto." They accept Bitcoin — the one with a public traceable ledger that Chainalysis and the FBI follow routinely. They didn't accept Monero at all until September 2025, and even then only through a third-party middleman, not natively.
The 'privacy company's' answer to "you doxed a user through their payment info" is "you should have paid us with a method we barely support."
This isn't the first time. In 2021, Proton logged and handed over the IP address of a French climate activistlogged and handed over the IP address of a French climate activist to French authorities via Europol. You have to be living under a rock not to heard of that story. In 2024, they gave Spanish authorities a recovery email addressgave Spanish authorities a recovery email address that led to the identification of a Catalan independence activist. French climate activist. Catalan independence activist. Stop Cop City protester.
Three activists, three countries, three MLAT requests, three times Proton complied and someone got identified. It's a pattern.
And none of this is ancient history or edge cases. This is the story of a company that has handed over user data in response to over 40,000 government orders since 2017, maintains a 94% compliance rate, markets "not even Proton" can access your data while their own privacy policy says they scan incoming emails before encrypting them, and just got caught helping the FBI identify a protester whose crime was standing on the wrong piece of dirt.
I pay for a Proton account. I've spent hours going back and forth with die hard Proton fans and Proton on X, including directly with their CEO. I've read every word of their privacy policyprivacy policy, their terms of serviceterms of service, their transparency reporttransparency report, their marketing pages, and their data processing agreement. This is NOT a "Proton is worse than Gmail" argument Gmail reads everything you send and sells profiles based on it.
What Proton does is market itself as a mathematical privacy guarantee while operating a compliance machine that rubber-stamps nine out of every ten government data requests it receives. The people using Proton aren't switching from Outlook for better fonts. They're switching because they were told their data would be untouchable even if not directly but through there marketing.... I'll explain, but it's not.
Proton's own transparency reporttransparency report, when you put it in a table instead of a press release:
The Numbers They Published Themselves
From 2017 to 2025, Proton received 45,667 legal orders for user data. They complied with 40,389 of them. In 2017, they got 26 orders. In 2024, they got 11,023, and they complied with 10,368. That's a 423x increase in seven years. The contest rate peaked at 21.2% in 2021 when the French activist case put them under public scrutiny, then collapsed to 5.9% by 2024 as order volume nearly doubled. Martin SteigerMartin Steiger, a Swiss attorney who tracks Proton's reports, attributes part of the 2024 spike to Switzerland switching from per-request billing to a flat-rate compensation model for law enforcement data requests at the start of that year. Less friction for cops to file requests means more requests get filed. Proton got bigger, the government made requests cheaper, and the contest rate cratered.
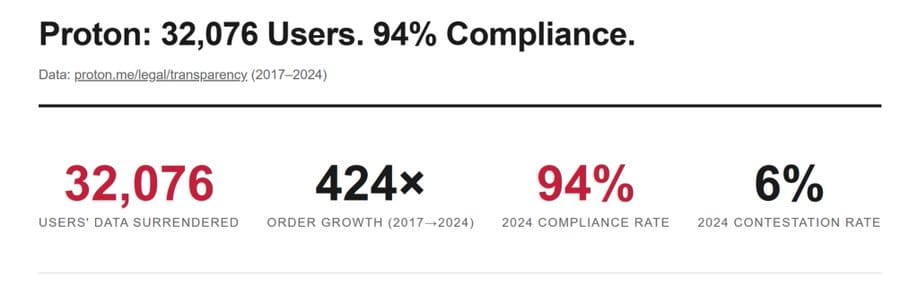
Protons own numbers, these are old it's over 40,000 now.
A 6% contest rate means they rubber-stamp 94% of requests without a fight. If your lawyer won 6% of your cases you'd fire them. But when Proton does it, it's "Swiss privacy."
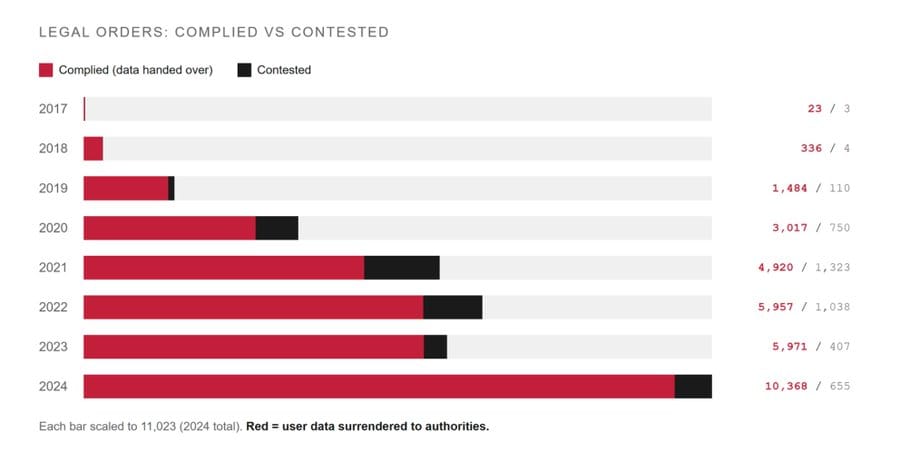
Legal Orders: Complied vs Contested
Do they fight, or bend over?
And before anyone says "they have to comply, it's the law," I need you to understand something. If compliance were mandatory, the rate would be 100%. It's not. That 6% they do contest proves that fighting is legal, it's an option, they just rarely use it. OVPN beat a Swedish court order back in 2021. Mullvad got raided by Swedish police who left empty-handed because there was nothing to find. The claim that resistance is impossible is cope for companies that choose cooperation.
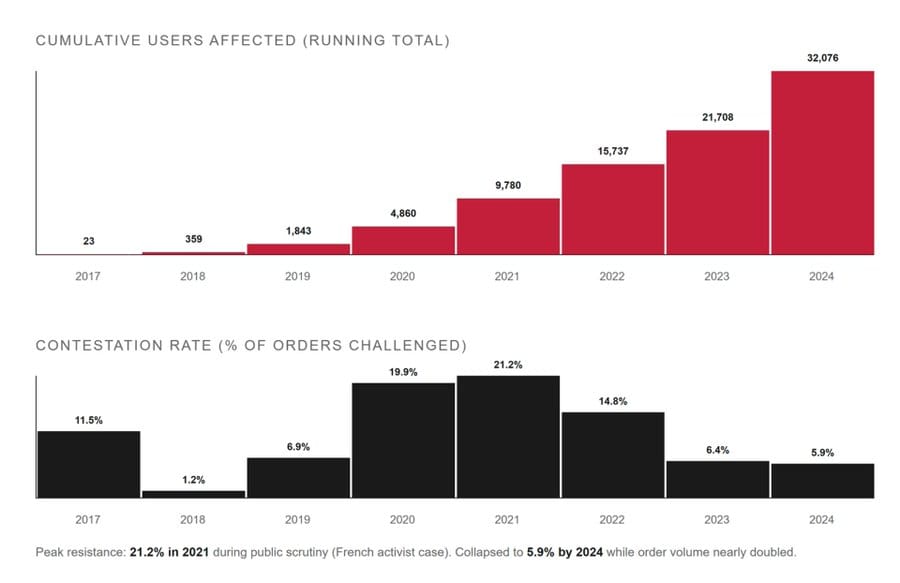
Cumulative Users Affected vs Contestation Rate
Now compare that to Proton's own VPN product, which denied 100% of all orders every single year from 2020 to 2025. Every one. Because Proton VPN actually has no logs to hand over. The architecture makes compliance impossible. Proton Mail's architecture does not. And that gap between "can't" and "won't" is the entire story.
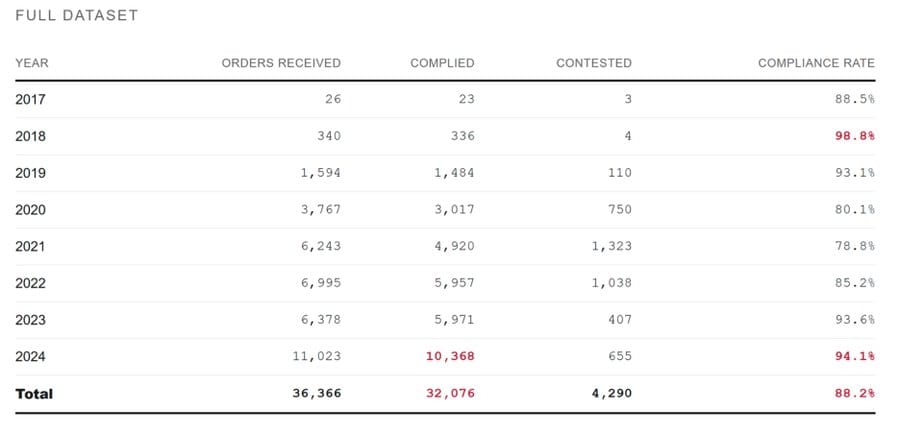
Yearly Data Set
Or compare it to TutaTuta, operating under German law. Not Switzerland, not some privacy utopia, Germany. Tuta's transparency report for the second half of 2025 shows they received 220 requests and complied with 58, a rejection rate of about 75%. In the first half of 2025, they received 227 requests and complied with 54. Tuta fights three out of four requests. Proton folds on nineteen out of twenty. And Tuta does it by lodging objections against requests based on the assumption that they're a telecommunications service, which the Court of Justice of the European Union ruled they're not. In other words, Tuta found a legal angle and uses it aggressively. Proton apparently hasn't found one, or hasn't looked.
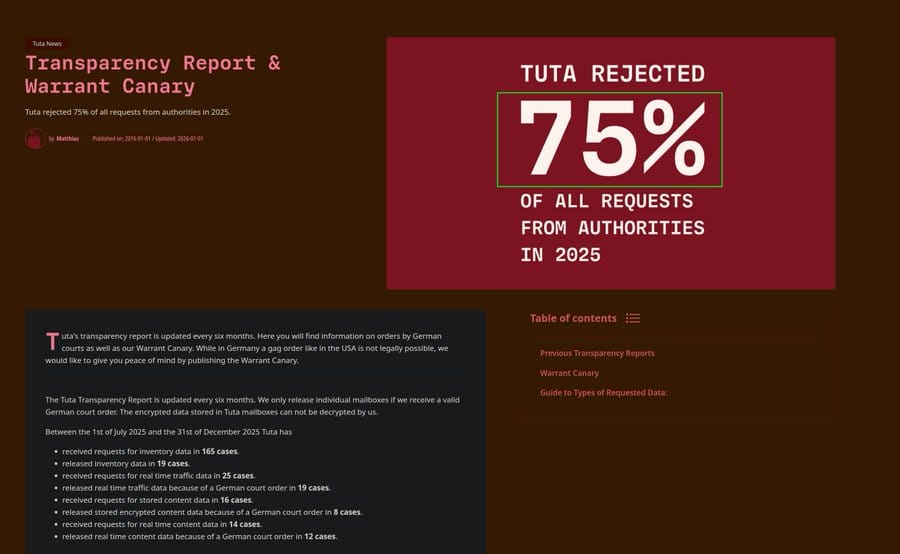
I'm no fan of Tuta (series in the works for them)
but the rates for them are night and day.
“Zero-Access” Means Zero Access to Data at Rest, Not Zero Access to Your Emails
If size explains the problem, Proton's business model is self-defeating. They take money to protect users, grow too big to protect them, and the advice becomes "use someone smaller." Their contest rate dropped from 21% in 2021 to 6% in 2024 while order volume doubled. They got bigger and fought less.
Proton's marketing page, word for word: "Proton Mail's zero-access architecture means we can never access your emails. As a result, we cannot hand your emails over to anyone."
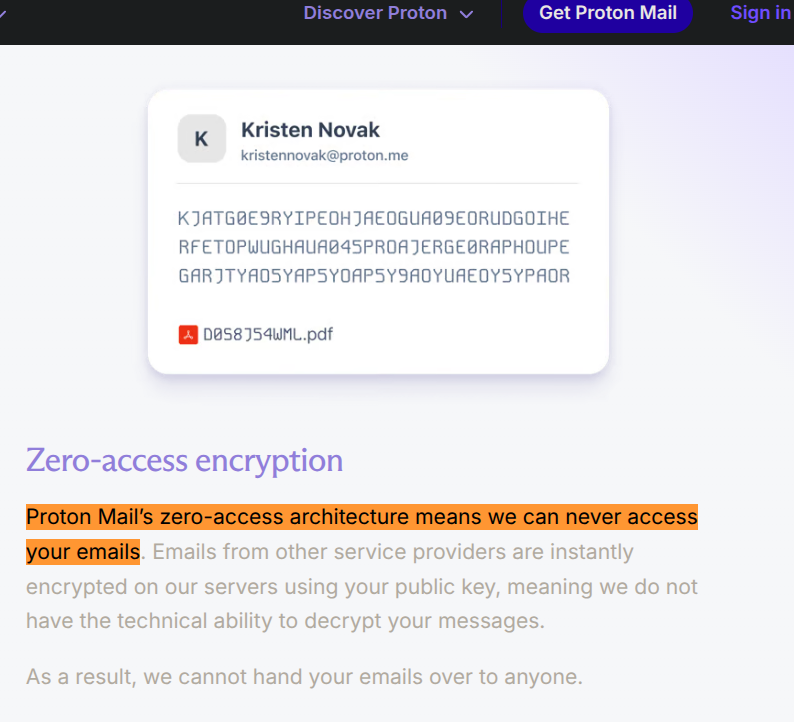
"Zero-Access"
Their homepage: "Our end-to-end encryption and zero-access encryption mean that no one (not even Proton) has the technical means to access your data without your permission. At Proton, privacy isn't a promise, it's mathematically ensured."
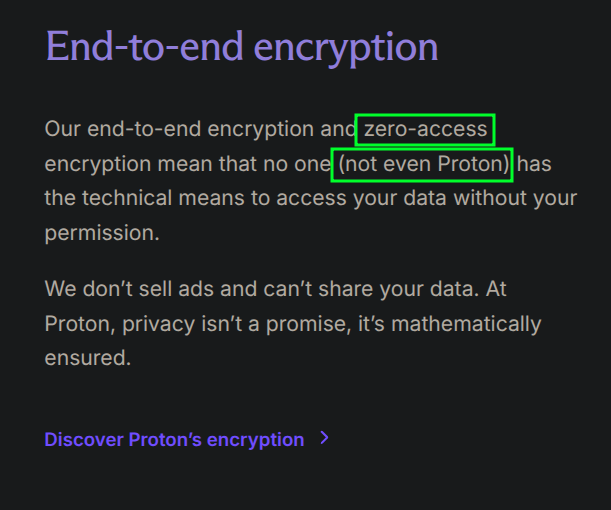
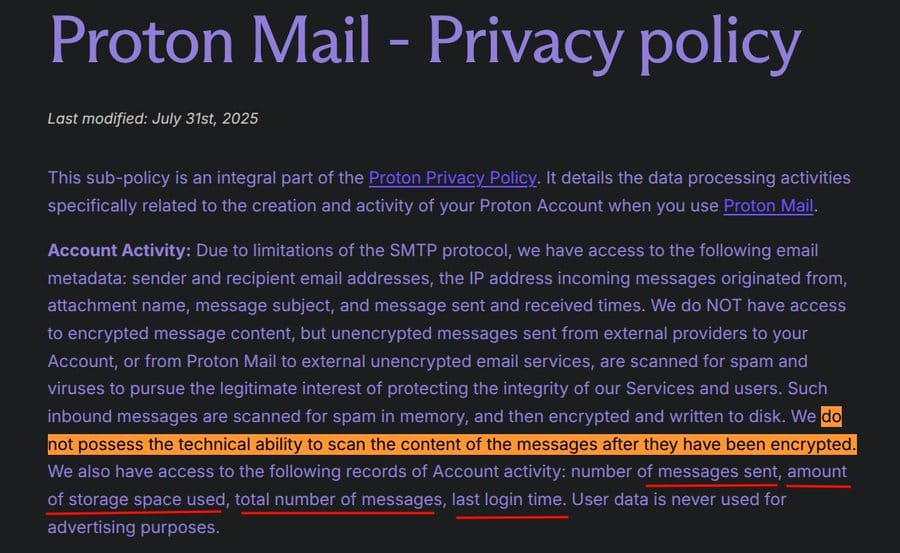
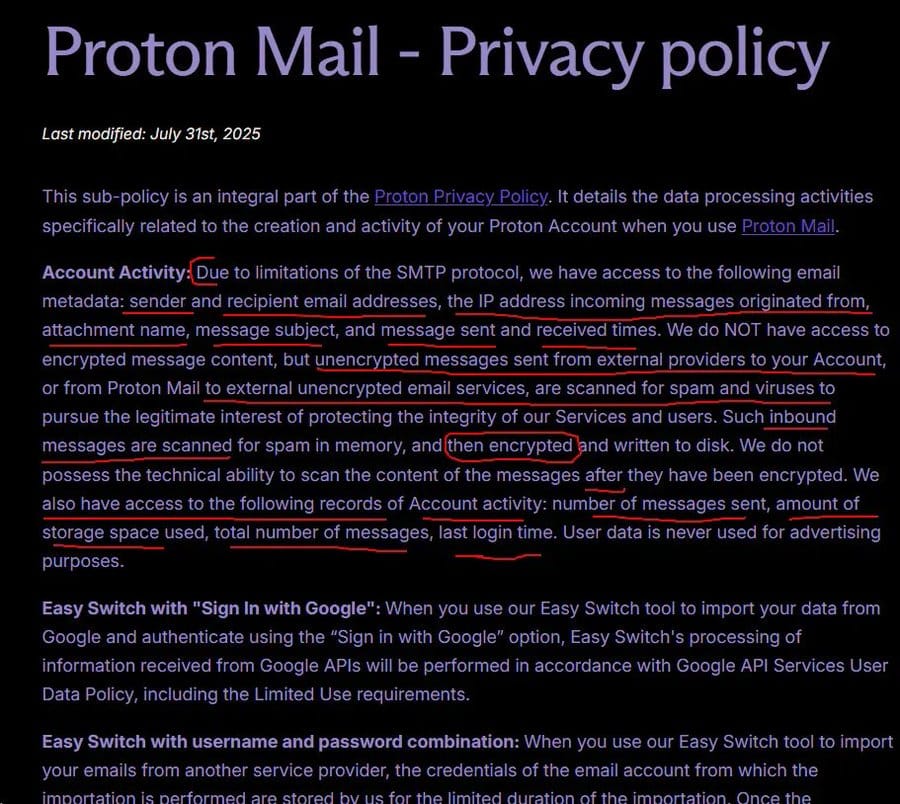
Now their own privacy policyprivacy policy, also word for word: "unencrypted messages sent from external providers to your Account, or from Proton Mail to external unencrypted email services, are scanned for spam and viruses... Such inbound messages are scanned for spam in memory, and then encrypted and written to disk."
Proton admitting they see email content before encrypting
They scan your incoming emails. In memory. Before encrypting them. Proton's servers see the plaintext content of every email that comes from a non-Proton sender, which is the vast majority of email traffic, because most people don't use Proton. When your bank sends you a statement, Proton reads it before they encrypt it. When your lawyer sends you privileged correspondence from their Gmail, Proton's servers see it in cleartext before it ever touches "zero-access encryption." When a source sends a journalist a tip, Proton sees it before the journalist does.
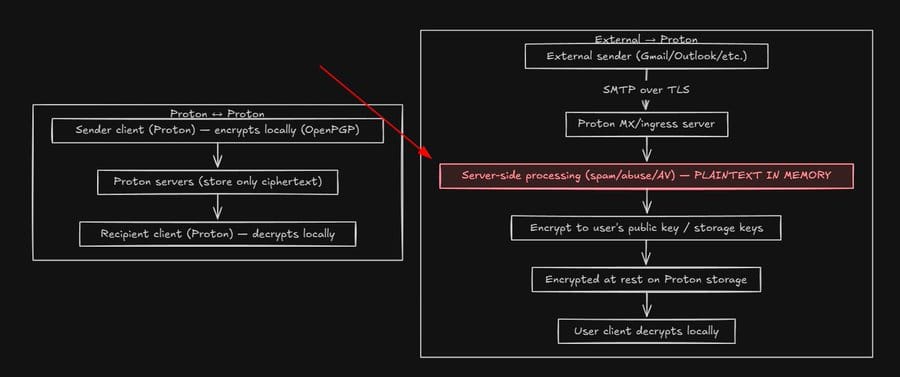
Proton themselves admitted this publicly. Their official account on X posted: "we briefly see the contents of the email before immediately and automatically encrypting it without ever being able to access it again." They called it a "limitation imposed upon us by providers like Gmail who do not use PGP encryption by default."
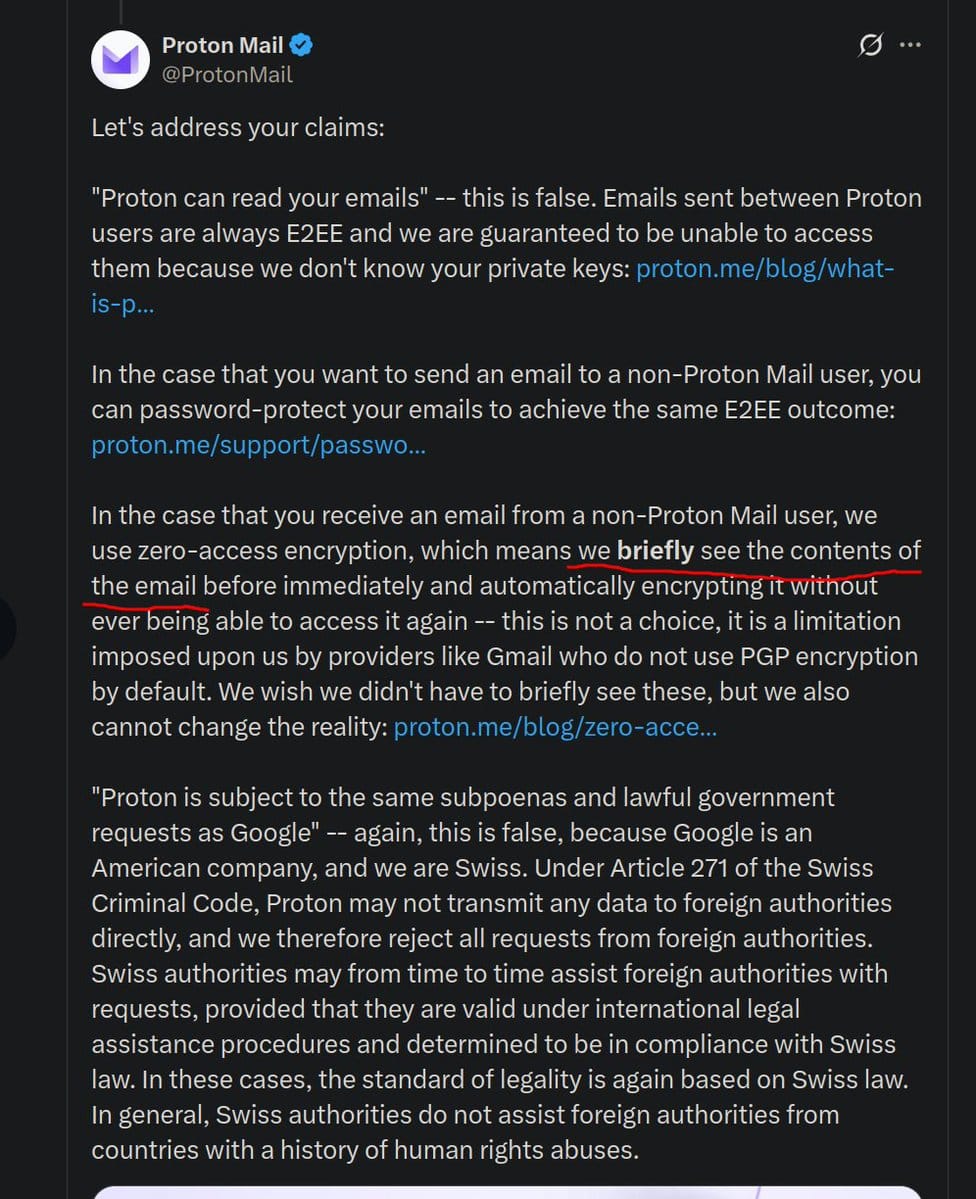
That's a great excuse, except it demolishes your own marketing. You can't say "not even Proton" can see your data and then admit you see every non-Proton email before encrypting it. Those two things are mutually exclusive.
And the "it's only in memory" defense doesn't hold up either. Whether you keep it for a millisecond or a millennium, access is access. Hiding behind "it's only in memory" is like saying you didn't rob the bank because you only held the money for a few seconds.
The marketing says "can't." The architecture says "can, but briefly." Those aren't the same thing.
chompie, the head of IBM X-Force Offensive Research, put it more directly in a tweet that got 1.1 million views: "Not only can Proton Mail read your emails, but they're subject to the same subpoenas and lawful government requests as Google. Real privacy requires end-to-end encryption, which users have to actively adopt, and most don't because it's hard and annoying."
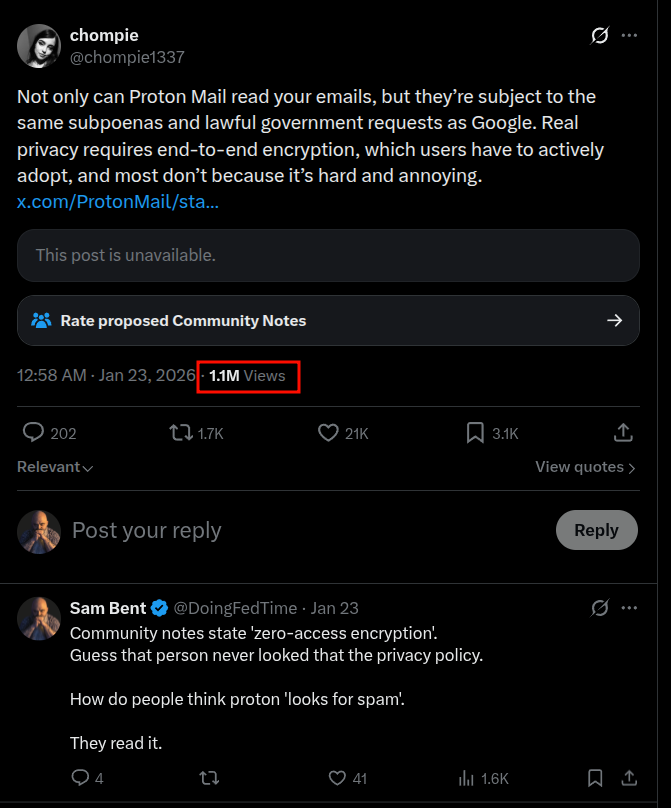
They read it, they say it.
Credit: @chompie1337@chompie1337
Their spam filtering tells the same story. They claim they "do not possess the technical ability to scan the content of the messages after they have been encrypted."
https://proton.me/mail/privacy-policyhttps://proton.me/mail/privacy-policy
That's true. But they explicitly do scan them before encryption. Proton runs body-level filtering for phishing links and content patterns, which means they're reading your inbound mail before they encrypt it. Header analysis alone would let most spam through. Their spam filtering system literally requires reading message content to function, which proves they have routine access to user communications. You can't run a content-level spam filter without reading the content. That's how email works, moreover it's how reading works, here read this invisible sentence to prove it:
What Proton Can Actually See
Their Mail privacy policyMail privacy policy lists everything they have access to, and it's not short.
https://proton.me/mail/privacy-policyhttps://proton.me/mail/privacy-policy
Email metadata, always accessible to Proton: 1. sender and recipient email addresses, 2. IP addresses of incoming messages, 3. attachment names, 4. message subjects, 5. message sent and 6. received timestamps, 7. number of messages sent, 8. storage space used, 9. total number of messages, and 10. last login time. Go ask an intelligence analyst if they would rather have that or the content of the message. (They will say the former)
Note that message subjects are not encrypted. Your subject lines, which often contain the most descriptive summary of what an email is about, are visible to Proton at all times. Every email you've ever sent or received through Proton, the subject line is accessible. "Re: Meeting with lawyer about divorce." "Your prescription refill." "Whistleblower submission." All visible. All metadata they can hand over.
Account information: any recovery email address or phone number you provided, account creation date, and device identifiers.
Calendar metadata is also not encrypted: 1. event start and 2. end times, 3. time zones, 4. repetition rules, 5. event creation and 6. update times, 7. event status. Your schedule, unencrypted.
Drive metadata too: 1. file and folder creation and 2. modification times, 3. permissions, 4. the username that created or 5. uploaded files, and 6. for shared URLs, 7. the creation time, 8. last access time, 9. number of accesses, and 10. creator.
Sender addresses, recipient addresses, subjects, attachment names, timestamps, IPs of incoming messages, recovery emails, recovery phones, device IDs, login history, storage used, message counts. That's what Proton "technically has." That's what 40,389 orders have requested since 2017. And that's practically everything except email content, which, as we've established, they can access if the sender email isn't a Proton one.
I have the Wayback Machine for this one (they tried to erase it).
The IP Logging They Tried to Hide
In January 2021, Proton's homepage stated, and I'm quoting the archived versionarchived version: "No personal information is required to create your secure email account. By default, we do not keep any IP logs which can be linked to your anonymous email account. Your privacy comes first."
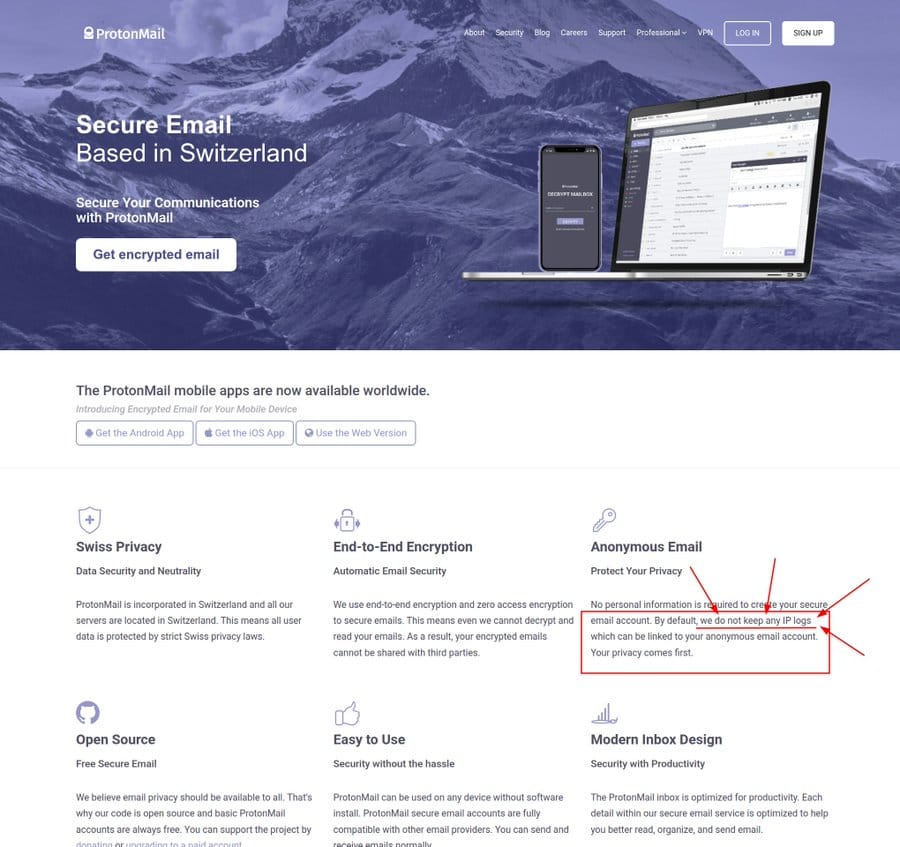
Proton's homepage, January 2021 Wayback Machine archive
https://web.archive.org/web/20210104131534/https://protonmail.com/https://web.archive.org/web/20210104131534/https://protonmail.com/
Then in the summer of 2021, it came out that Proton had logged and handed over the IP address of a French climate activist to French authorities via Europol and Swiss legal assistance channels. The activist was part of Youth for Climate, an environmental group that occupied buildings in the Place Sainte Marthe area of Paris. Swiss authorities received the request, approved it, and Proton was compelled to start logging the IP address of that specific account going forward. That IP, combined with the recovery email Proton also provided, led to an Apple ID, which led to the activist's identification and arrest.
After this became public in September 2021, Proton quietly scrubbed their website. The "we do not keep any IP logs" language vanished. In its place: "ProtonMail is email that respects privacy and puts people (not advertisers) first. Your data belongs to you, and our encryption ensures that." No mention of IP logs. No mention of what happened. They just deleted the claim and hoped nobody noticed.
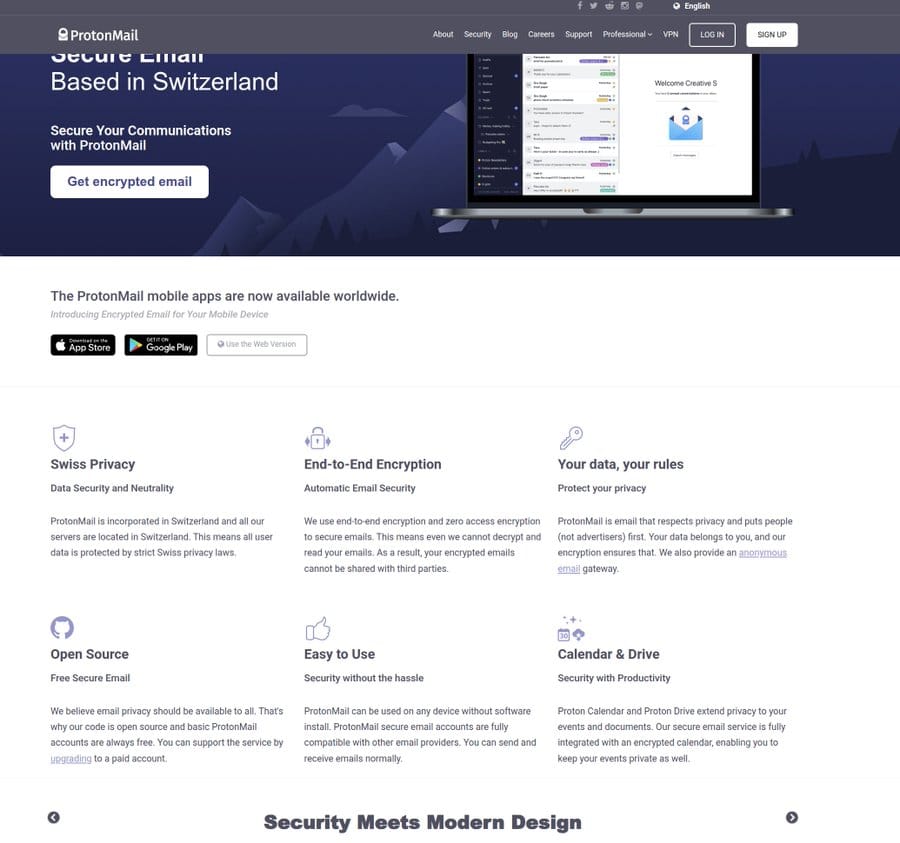
Proton's homepage, October 2021 Wayback Machine archive
https://web.archive.org/web/20210930230626/https://protonmail.com/https://web.archive.org/web/20210930230626/https://protonmail.com/
The RegisterThe Register documented this with Wayback Machine comparisons. Bruce SchneierBruce Schneier, arguably the most respected cryptographer alive, wrote a blog post titled "ProtonMail Now Keeps IP Logs." Proton's updated privacy policy now says: "If you are breaking Swiss law, ProtonMail can be legally compelled to log your IP address as part of a Swiss criminal investigation."
And buried on a VPN support pageVPN support page, not the homepage, not the privacy policy summary, not anywhere a normal user would look, Proton admits: email "is generally not no-logs and can require IP disclosure in the event of a Swiss criminal investigation. That's why if your threat model requires hiding your IP from Swiss authorities when using Proton Mail, we recommend using a VPN or Tor."
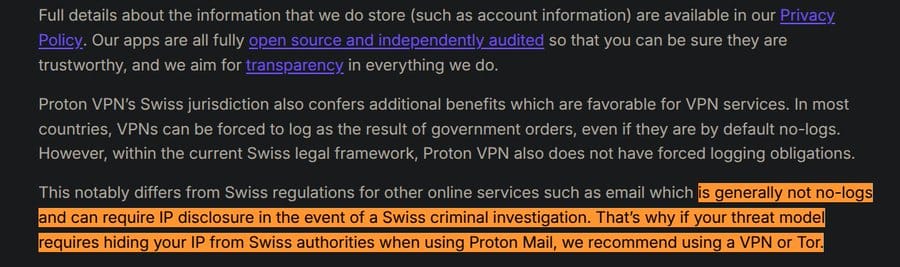
https://protonvpn.com/support/no-logs-vpnhttps://protonvpn.com/support/no-logs-vpn
Proton is telling you, on their own website, that Proton Mail doesn't protect your IP from Swiss authorities. Their solution? Buy their VPN too. The privacy product has a gap, and the fix is another purchase. But won't your purchase still be recorded? Yes. But don't worry, here are some buzzwords to make you feel safe: Swiss law, zero knowledge, privacy, transparency, open source, and full disk encryption. See? All better, now hit buy, and heart our stupid 1,000th post about Gmail.
In September 2025, Phrack Zine, one of the oldest and most respected hacking publications on the internet, had their Proton accounts suspended. Phrack has been publishing since 1985. It predates Google, it predates most of the people working at Proton, and it's one of the foundational texts of the hacking and security research community. And Proton nuked their accounts because a CERT sent them a tip.
Not a court order or a subpoena, also not some legal order of any kind. A CERT advisory. CERTs are advisory bodies. They issue recommendations. They have ZERO LEGAL enforcement authority.
They are not law enforcement, they are not courts, and their tips carry exactly as much legal weight as a Reddit comment.
The Phrack Incident: Suspend First, Investigate Never
The Intercept broke the full story.The Intercept broke the full story. Two journalists publishing under the pseudonyms Saber and cyb0rg had their accounts suspended. They were reporting on a sophisticated hacking operation into South Korean government systems, including the Ministry of Foreign Affairs and the military's Defense Counterintelligence Command, attributed to Kimsucy, a North Korean state-backed hacking group. They were doing responsible disclosure, they had notified KrCERT/CC (South Korea's CERT), and they were using Proton specifically because they're journalists working on sensitive national security reporting.
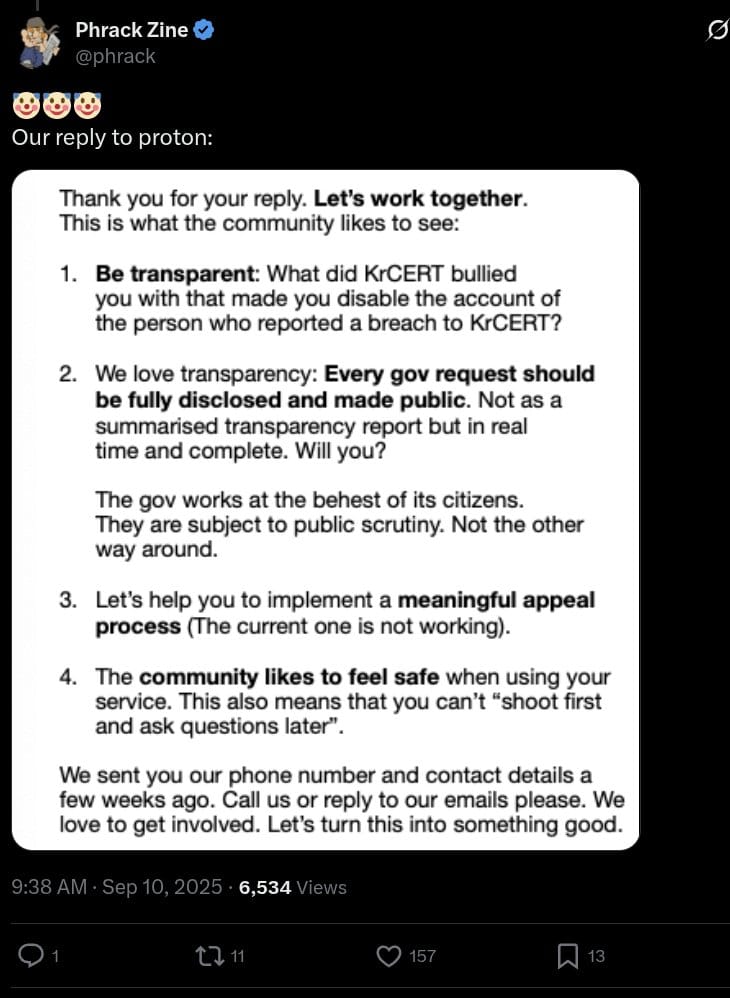
https://x.com/phrack/status/1965771989748220048?s=20https://x.com/phrack/status/1965771989748220048?s=20
Proton suspended their dedicated disclosure email account. Then, the next day, suspended Saber's personal Proton account too. On August 22nd, Phrack editors emailed Proton requesting restoration. No response. On September 6th, they sent a follow-up. Still nothing. On September 9th, Phrack went public on X, asking "why Proton was cancelling journalists and ghosting us." Only then, on September 10th, did Proton respond.
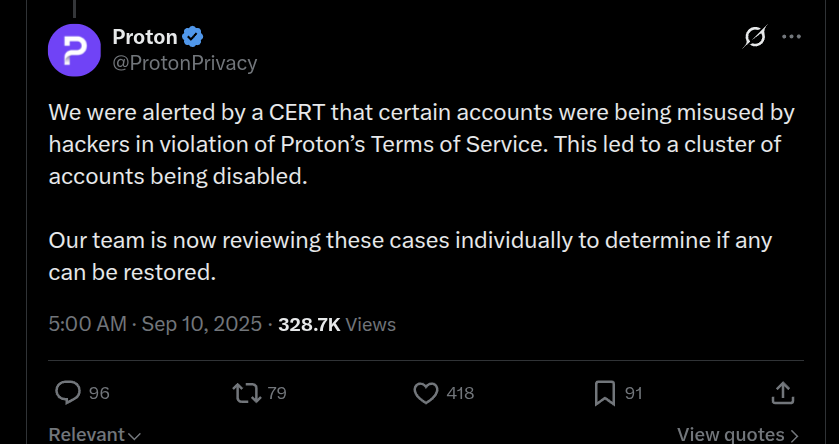
Proton's response: "We were alerted by a CERT that certain accounts were being misused by hackers in violation of Proton's Terms of Service. This led to a cluster of accounts being disabled."
https://x.com/ProtonPrivacy/status/1965701997304103394?s=20https://x.com/ProtonPrivacy/status/1965701997304103394?s=20
A "cluster" of accounts. Proton didn't verify which accounts were legitimate and which weren't. They didn't investigate before acting. They cluster-banned everyone in the vicinity of the CERT tip and called it enforcement. Phrack reported sending eight emails to Proton. Proton claimed they only received two. Appeals were rejected or ignored. Proton's own appeal process failed, and the accounts were only restored after the story started getting attention on social media.
The Freedom of the Press Foundation's deputy director stated that "journalists are among the users who need these and similar tools most." Phrack requested assurance that "Proton does not disable accounts unless Proton has a court order or the crime (or ToS violation) is apparent." They never got that assurance.
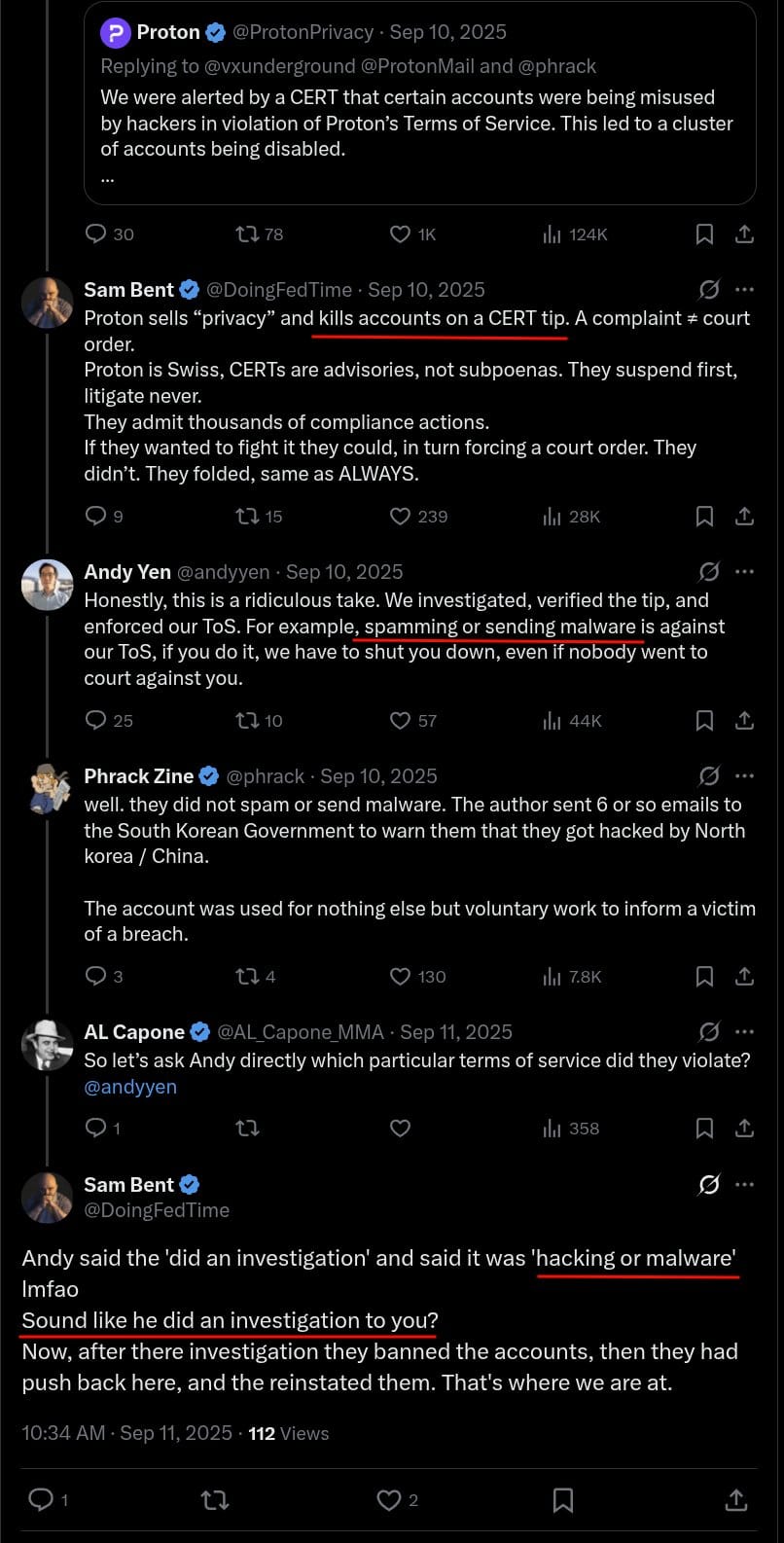
Andy Yen, Proton's CEO, jumped in to defend it: "Honestly, this is a ridiculous take. We investigated, verified the tip, and enforced our ToS."
https://x.com/DoingFedTime/status/1965729387531165939?s=20https://x.com/DoingFedTime/status/1965729387531165939?s=20
Yelling at proton's CEO who doesn't know what's going on.
Is it spamming? Is it Malware?
Except if the investigation verified the tip, why did they reinstate the accounts? If the accounts were legitimately violating the ToS, restoring them makes no sense. And if they weren't violating the ToS, then Proton suspended legitimate accounts for weeks based on unverified gossip from a non-legal entity, ignored their appeals, and only fixed it when the internet started watching. Both options are bad.
And here's the zero-access paradox. Proton's privacy marketing says they can't see what's in your account because of zero-access encryption. But they also claim they "investigated" account activity to enforce ToS violations. You can't have both. Either you can see what users are doing, or you can't. If you can, the zero-access claim is false. If you can't, the "investigation" claim is false. When I called this out on X, the CEO couldn't even state whether the alleged violation was "malware or hacking." He didn't know. Because there was no real investigation. They just cluster-banned on a tip and made up a justification after the fact.
FADP (Swiss Federal Act on Data Protection) confidentiality protections weren't invoked in this case because no court ordered anything. Proton acted on a voluntary CERT tip without legal compulsion. They chose to do this. And their Terms of Service give them the cover: "The Company may also terminate Accounts which are being used for illegal activities that are not listed above, particularly in response to orders from the competent authorities informing of such illegal activity." But a CERT is not a "competent authority." A CERT is an advisory body. Proton treated a suggestion like an order.
Swiss Privacy: The Brand, Not the Shield
Proton markets Swiss jurisdiction like it's a force field. Their blog says Switzerland is "outside of US and EU jurisdiction," that Swiss companies "cannot be compelled to engage in bulk surveillance," and that "the laws of mathematics cannot be changed or altered." This is true in the narrow sense that Swiss law provides process protections, meaning foreign governments can't just email Proton and demand data. Requests have to go through Swiss legal channels.
Those Swiss legal channels have produced 40,389 complied orders in eight years. The process protection amounts to a Swiss stamp on the request before Proton hands over your metadata. A stamp, congrats that's the protection.
Proton's policy says they'll challenge requests "whenever possible" and "where there are doubts as to the validity." Those are weasel words that give them total discretion over when to fight and when to fold. Their numbers show they fold on about 90% of requests. "Whenever possible" apparently means "almost never."
And here's something most people don't realize. The US, the EU, whoever, they don't need to subpoena Proton directly. They go through Mutual Legal Assistance Treaties. The request goes from a foreign government to Swiss authorities, Swiss authorities rubber-stamp it, and Proton complies. That's how the French activist case worked. That's how the 40,000+ orders worked. "Swiss jurisdiction" doesn't mean unreachable. It means there's one extra step in the chain, and that step has a 94% pass rate.
Proton's homepage used to sell "no IP logs" until 2021. That pitch went way beyond "protection from data brokers." They were explicitly marketing anonymity. After they got caught logging an activist's IP, they walked it back, but the marketing damage was already done. Millions of people signed up based on claims Proton no longer makes.
Proton also doesn't notify users when their data gets requested. Steiger LegalSteiger Legal flagged this: Proton claims it's the Swiss authorities' responsibility to inform targets, not theirs. So your data gets handed over and you don't even find out unless you get arrested or read about it in 404 Media.
And despite all the talk about Swiss data sovereignty, Proton routes your support tickets through Zendesk in the United States. Your payment data goes through Chargebee, Stripe, and PayPal, all US companies. Customer support is also processed through Atlassian, which operates in the EU, US, and UK. Sales data goes through HubSpot in the US. And their own customer support subsidiaries are in Macedonia and Taiwan.
So your encrypted email sits in Switzerland, but your support conversations, payment records, and sales interactions get processed across five different countries by six different third-party companies, most of them American. "Swiss privacy" has some pretty big asterisks.
Privacy Company Requires You to De-Anonymize Yourself to Sign Up
Try to create a Proton account over Tor or a VPN. Go ahead. Proton runs what they call an "intelligent algorithm" that determines what verification method you get hit with during signup. If your IP looks like it's coming from a VPN or a Tor exit node, the algorithm escalates you from CAPTCHA to email verification to SMS phone verification. A privacy company demands your phone number because you tried to sign up privately.
Proton says this is to "prevent spam bots", and that's a real problem. Spammers creating bulk accounts would get Proton's mail servers blacklisted by Gmail and Outlook. But the result is that the exact users Proton markets to, people who route their traffic through Tor because they need anonymity, are the ones most likely to be forced to hand over a phone number to create an account. And Proton's privacy policy says phone numbers used for verification are "saved temporarily" and then stored as a "cryptographic hash." "Temporarily" is undefined. And a cryptographic hash of a phone number is trivially reversible because the input space is small, there are only so many valid phone numbers in the world.
VoIP and virtual numbers are also blocked. Proton's filters reject about 60% of traffic from known VoIP ranges. So you can't even use a burner number. If you want a Proton account and you're coming from Tor, you're either giving them a real phone number tied to your identity or you're emailing their support team to beg for an exception. "Privacy by default" apparently doesn't apply to the signup page.
MullvadMullvad? You click "generate account," get a 16-digit number, done. No email, no phone, no name, no CAPTCHA. TutaTuta? CAPTCHA and you're in, no phone number required. The idea that privacy-focused signup and anti-spam are mutually exclusive is a design choice, not a law of physics. Other companies figured it out. Proton chose not to.
Proton Business VPN: The Quiet Admission
Proton's consumer VPN claims a strict no-logs policy, and their transparency report backs it up with a 100% denial rate on all VPN orders. But Proton's Business VPN productBusiness VPN product, documented in their Business Privacy Policy, collects connection and disconnection timestamps, device type and operating system, and the IP address used to connect to VPN servers.
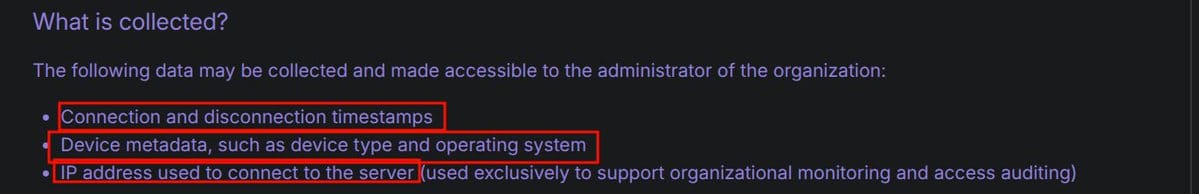
https://proton.me/business/privacy-policyhttps://proton.me/business/privacy-policy
That's the exact data they swear their consumer VPN never logs. The existence of this feature proves Proton has the technical capability to log VPN connections. The no-logs claim for consumer users is a business decision, not a technical limitation. They built the logging infrastructure. They deployed it for business customers. They just tell consumer users it's turned off. Trust them.
The Bitcoin Wallet from the Privacy Company That Wouldn’t Accept Monero
In 2023, Proton launched Proton Wallet. A Bitcoin wallet. Bitcoin, the cryptocurrency with a public, permanent, fully traceable blockchain where the FBI has recovered millions from ransomware operators just by following the ledger. Chainalysis and Elliptic have built entire companies around tracing Bitcoin for law enforcement. Every transaction is visible to anyone who looks. And this is what the privacy company chose to build a wallet for.
Meanwhile Monero exists and they wouldn't even accept it as payment. MullvadMullvad accepts it. IVPN accepts it. Proton didn't accept Monero at all until September 2025, and even then only through a third-party middleman called ProxyStore, not natively. David Peterson, their VPN general manager, promised direct Monero integration "by the end of Summer 2025." Missed that deadline. Users have been begging for it on Proton's UserVoice forum for years.
So they built an entire wallet product around the surveillance coin, then dragged their feet for years on accepting the privacy coin as payment. They'll build you a Bitcoin wallet but they won't let you pay them with Monero directly. That tells you everything about where their priorities actually are.
$100 Million and a CERN Pedigree
Proton pulls in over $100 million a year in revenue. They have 585 employees. Their primary shareholder is the Proton FoundationProton Foundation, a Swiss nonprofit that Andy Yen, co-founder Jason Stockman, and their first employee Dingchao Lu endowed with Proton shares. This is marketed as a guarantee of mission integrity. "No VC investors" means no pressure to monetize users, they say.
A nonprofit shareholder doesn't change the compliance numbers or what the privacy policy says about scanning emails. It doesn't change the 40,389 orders. The foundation structure prevents a hostile takeover and ensures "permanent adherence to the mission." The mission, apparently, includes a 94% compliance rate and cluster-banning journalists on CERT tips.
Andy YenAndy Yen has a PhD in particle physics from Harvard and did research at CERN on the ATLAS experiment before founding Proton in 2014. The Snowden revelations motivated him and his co-founders to build encrypted email. That origin story is genuine and it makes for a great TED talk. But a physics degree doesn't make your privacy policy honest, and working at CERN doesn't change the fact that your compliance rate is 94%.
Proton also received €2 million in EU funding through the Horizon 2020 program and spends up to €100,000 per year lobbying the EU through APCO Worldwide, a Washington DC-based lobbying firm (probably nothing, right?). Their lobbying focus areaslobbying focus areas include the Digital Markets Act, encryption, cybersecurity, and data retention. In December 2022, they met with Commissioner Ylva Johansson's cabinet about CSAM, the same policy area that the EU's Chat Control proposal targets. In March 2025, they met with EVP Stéphane Séjourné about AI competitiveness.
I'm not saying lobbying the EU on encryption policy is sinister. But when your marketing pitch is "scrappy Swiss scientists fighting Big Tech" and your lobbyist is APCO Worldwide out of Washington DC, those two stories don't live in the same universe.
The Political Neutrality Question
In January 2025, Andy Yen posted on X that "10 years ago, Republicans were the party of big business and Dems stood for the little guys, but today the tables have completely turned." Then Proton's official Reddit account piled on with: "Until corporate Dems are thrown out, the reality is that Republicans remain more likely to tackle Big Tech abuses."
The CEO of an encrypted email service used by journalists, whistleblowers, and political dissidents, people whose safety depends on the platform being genuinely neutral, publicly praised the incoming ruling party. And then his company's official account amplified it. After backlash, Proton deleted the Reddit comment and blamed "internal miscommunication." The Intercept covered the story.The Intercept covered the story. Yen said he'd stop sharing political opinions going forward.
But the damage is already done. If you're a journalist investigating the Trump administration and your encrypted email provider's CEO is out here cheerleading the Republican Party, that's not an abstract concern. Instead, your threat model's telling you to pay attention. And "internal miscommunication" is corporate for "we said the thing we shouldn't have,out loud and it didn't go well."
The Affiliate Machine
Proton runs a partner and affiliate programpartner and affiliate program offering up to 100% commission on referrals with recurring revenue on renewals. No doubt EVERYONE discloses this, when shilling or sticking up for them. Their partner page says: "Boost credibility and engage your privacy-conscious followers by endorsing secure digital solutions." They recruit MSPs, MSSPs, content creators, and influencers, and they have a dedicated contact at influencers@proton.ch.
A significant portion of the "privacy recommendation" ecosystem that tells you to use Proton is financially incentivized to tell you to use Proton. When your favorite privacy YouTuber says "I recommend Proton Mail, link in the description," that link is probably paying them a recurring commission. They're not lying about Proton being better than Gmail. They're just leaving out everything I've written here, because it's hard to sell "better than Gmail but not what the marketing says" when you're getting paid per signup.
And when I posted Proton's own transparency numbers on X, the response was telling. People didn't argue with the numbers. They argued with me for posting them: "Your post is negative." "You're scaring people away from Proton." "You don't understand privacy vs anonymity."
One person wrote an entire essay debunking arguments I never made: that encryption was compromised (never said that), that Proton shouldn't comply with legal orders (never said that), that users should switch to Gmail (never said that). They invented claims, then argued against them solo. I posted Proton's own numbers and screenshots of marketing language they deleted. The numbers are the numbers.
HideMyAss: We’ve Seen This Movie Before
In 2011, HideMyAss VPNHideMyAss VPN was one of the most popular VPN services in the world. Their website said "anonymous VPN," "hide your IP address," "surf anonymously," "anonymously encrypt your entire internet connection." Sound familiar? Same promises Proton makes today. Same marketing playbook.
Then the FBI came knocking. Cody Kretsinger from LulzSec used HideMyAss to hack Sony Pictures. UK court order lands, HideMyAss hands over connection logs, timestamps, IP addresses, everything the FBI needed to arrest him. Turns out HideMyAss had been logging the entire time. They later admitted in a blog post that they logged connection times and IPs to deal with "abusive users." They marketed anonymity while recording everything.
This is the pattern. Company markets privacy guarantees that sound absolute. Users trust those guarantees with their safety. Legal pressure shows up and the company folds because the architecture always allowed it. The people who needed the guarantees most are the ones who get burned. HideMyAss promised anonymity and kept logs. Proton promises "not even Proton" can see your data and scans your emails before encrypting them. Different company, same gap between the marketing and the architecture, same users finding out too late.
HideMyAss eventually hired an auditor to verify a real no-logs policy. By then nobody cared because the trust was gone. Marketing claims are not architectural guarantees. Figure out which one you're relying on before you need it, not after.
What Privacy Actually Looks Like
If you want email privacy that doesn't depend on trusting a company's marketing, use PGP. You can use PGP with any email provider, including a self-hosted one. The encryption happens on your machine, before it touches any server, and only the recipient can decrypt it. No company sees your plaintext. No "scanning in memory." No zero-access marketing with an asterisk. You can use PGP anywhere, including on an X post if you want. It doesn't require a specific provider.
If you want a VPN that can't identify you even if every government on earth shows up with warrants, MullvadMullvad generates a random 16-digit account number with no email, username, password, identity. They accept Monero and cash in the mail. When Swedish police raided them, they left empty-handed because there was literally nothing to find. That's not a no-logs policy, that's a no-knowledge architecture. There's a difference. If you lose your 16-digit number, your account is gone forever, because there's no recovery mechanism tied to your identity. Mullvad doesn't know who you are, so they can't log you even when governments show up demanding it.
You can self-host all of this. Email, VPN, password management, file storage. You don't have to rely on any company. The infrastructure exists. The tools are free and open source. If Proton's model of "trust us, we're Swiss" doesn't satisfy your threat model, the answer isn't a different company with a different trust-us pitch. The answer is removing the need to trust anyone.
If you want to keep using Proton because it's genuinely better than Gmail for most people, then keep using it. I pay for a Proton account myself. But use it with your eyes open. Don't use it because you think your data is "mathematically" protected. Don't use it because you think Switzerland makes you untouchable. And don't use it because a privacy influencer with an affiliate link told you it's the answer. Use it because it's a marginal improvement over Big Tech that still collects your metadata, still reads your incoming emails before encrypting them, still hands over data in response to 94% of government orders, and still cluster-bans journalists on CERT tips without a court order.
That's what you're buying. A brand with a privacy label on it.
Sources
Proton's own documents (cope shills)
Stop Cop City / FBI case (March 2026)
404 Media — original report404 Media — original report · CyberInsiderCyberInsider · Android PoliceAndroid Police · Steiger LegalSteiger Legal
French activist case (2021)
TechCrunchTechCrunch · The RegisterThe Register · Bruce SchneierBruce Schneier
Catalan activist case (2024)
TechCrunchTechCrunch · TechRadarTechRadar
Phrack journalist suspension (2025)
The InterceptThe Intercept
Political neutrality (2025)
The InterceptThe Intercept
IP logging — Wayback Machine archives
Before (Jan 2021)Before (Jan 2021) · After (Oct 2021)After (Oct 2021)
Comparisons
Tuta transparency reportTuta transparency report · Mullvad police raidMullvad police raid · HideMyAss archived pageHideMyAss archived page
Background
Steiger Legal — 2024 transparency analysisSteiger Legal — 2024 transparency analysis · CERN Courier — Andy Yen profileCERN Courier — Andy Yen profile · LobbyFacts — Proton EU lobbyingLobbyFacts — Proton EU lobbying
X threads referenced throughout
@ProtonMail@ProtonMail · @ProtonSupport@ProtonSupport · @andyyen@andyyen · @phraikiux@phraikiux · @chompie1337@chompie1337 · @PplsCityCouncil@PplsCityCouncil · @DoingFedTime@DoingFedTime
FAQ: The Counterarguments, Addressed
"They have to comply with Swiss court orders. Every company does." If compliance were mandatory, the rate would be 100%. It's not. Proton contested 21% of orders in 2021 and 6% in 2024. That 6% proves fighting is legal. OVPN beat a Swedish court order. Mullvad got raided and gave nothing. Proton chooses cooperation 94% of the time.
"They can only hand over metadata, not email content. Your emails are still encrypted." That metadata includes sender addresses, recipient addresses, message subjects, attachment names, timestamps, IPs of incoming messages, recovery emails, phone numbers, device IDs, login history, and storage usage. Subjects alone tell you what the email is about. And for inbound email from non-Proton senders, which is the majority of email traffic, Proton sees the plaintext content before encrypting it. Their own privacy policy says so.
"The in-memory scanning is just spam filtering. Every email provider does it." Every email provider doesn't market "not even Proton" can see your data. The scanning is standard. Claiming it doesn't happen while doing it is not.
"You're confusing privacy with anonymity." Proton's homepage said "we do not keep any IP logs which can be linked to your anonymous email account" until they got caught logging an activist's IP in 2021 and deleted it. They were the ones marketing anonymity, not me. I'm quoting their own deleted claims back at them.
"Swiss law protects users better than US or EU law." Swiss law produced 40,389 complied orders. Tuta, under German law, rejects 75% of requests. Proton, under Swiss law, contests 6%. Swiss jurisdiction adds one step to the chain. It doesn't stop the chain.
"Proton is still better than Gmail." Nobody said otherwise. Gmail is worse. But Proton doesn't market "slightly better than Google." They market mathematical privacy guarantees and zero-access encryption. When "at least we're not Google" is your best defense, you've already conceded the point.
"You're scaring people away from encrypted email." Accurate data isn't scary. These are Proton's own numbers from their own transparency report. If the facts hurt the brand, that's a product problem, not a reporting problem. People deserve to know what they're actually getting.
"They'd get shut down if they refused all orders." Nobody said refuse all orders. The issue is refusing only 6%, down from 21% when people were watching. The contest rate collapsed as public scrutiny faded and order volume doubled. They got bigger and fought less.
"The encryption is still end-to-end between Proton users." Correct. If both sender and recipient use Proton, the content is E2E encrypted and Proton can't read it. But most email traffic is between Proton and non-Proton users. Your bank, your employer, your doctor, your lawyer, most of them use Gmail or Outlook. Every one of those emails hits Proton's servers in plaintext before encryption. E2E between Proton users is real. It's also the minority of most people's email.
"CERTs have some authority. They're not just random tipsters." CERTs are advisory bodies. They issue recommendations. They have zero legal enforcement authority. They cannot compel account suspension. Proton's ToS says they act on "orders from the competent authorities." A CERT is not a competent authority. Proton treated a suggestion like an order, cluster-banned journalists, ignored appeals for weeks, and only fixed it after public pressure.
"They only gave up payment info, not email content. The system worked." A protester got identified and arrested because Proton handed over a credit card payment identifier. "Only payment info" was enough to unmask them. Proton routes payments through Chargebee, an American company, so your Swiss privacy email's payment data sits in US infrastructure. And Proton's own response said "Proton did not provide any information to the FBI" in one sentence and "only payment info was disclosed" two sentences later. If the system worked, it worked against the user. Proton's suggestion afterward was "use crypto or cash," but they don't natively accept Monero and they built a Bitcoin wallet instead. Their privacy architecture has a payment-shaped hole in it and their advice is to step around it yourself.
"Proton didn't give data to the FBI. Swiss authorities did." If I hand a loaded gun to someone, and that person shoots you, the fact that I didn't pull the trigger doesn't mean I didn't arm the shooter. Proton gave data to Swiss authorities knowing it was an MLAT request destined for the FBI. The French activist, the Catalan activist, and the Stop Cop City protester all got identified through the same pipeline. Proton is the first link in the chain every time.
"You just hate Proton." I pay for a Proton account. I've never said "don't use Proton." I posted their own numbers from their own transparency report and quoted their own privacy policy. If reporting what a company publishes about itself counts as hate, every financial analyst on Wall Street is a hater. I kick them in the teeth becasue they can do better.
"The compliance numbers include orders for accounts that don't exist." Proton's own report separates "complied" from "contested." If an account doesn't exist, there's nothing to comply with and nothing to contest. Those are different categories. The 94% compliance rate is among orders where data existed to hand over.
"No one will successfully deny 100% of legal orders." Proton VPN does. Every year. 100% denial rate from 2020 to 2025. The architecture makes compliance impossible. Proton Mail's architecture allows it, and they comply 94% of the time.
"You're just posting this for engagement." The post that started this had 258,000 views. I've spent months reading Proton's privacy policies, terms of service, and transparency reports. I've gone back and forth with their CEO on X. If I wanted easy engagement I'd post memes, not footnoted breakdowns of Swiss data processing agreements.