Apple Obeyed Russia and Britain in the Same Week
This week Apple pulled VPN apps in Russia at Roskomnadzor's request and forced UK users to hand over government ID to keep using their phones normally.
Two things happened inside Apple's platform this week that show why trusting a single company with your phone is a privacy trap.
On March 25, 2026, Apple pushed iOS 26.4 to UK users. The update landed overnight and included one change that nobody could opt out of: age verification tied to your Apple Account. To prove you're an adult, Apple's official support page requires a credit card, a driver's licence scan, or a PASS-scheme ID card. UK debit cards are rejected.
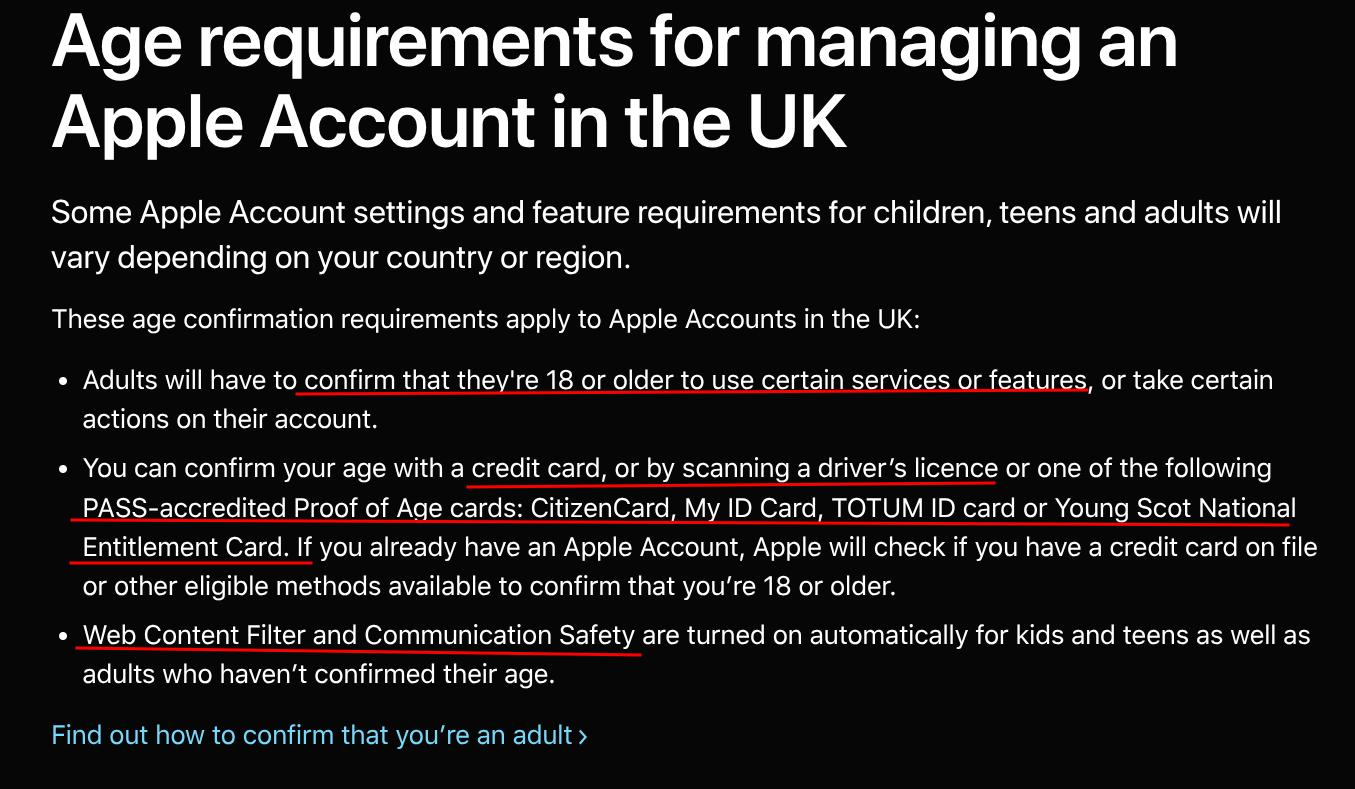
If you refuse to hand Apple your financial or government identification, your device gets child-level content restrictions applied automatically. Silkie Carlo, director of Big Brother Watch, called it "more like ransomware." The legal mechanism behind it is the UK Online Safety Act, enforced by Ofcom, which praised the rollout as "a real win for children and families," and noted that Ofcom had "worked closely with Apple" on the verification design, which is one way to describe the regulator that enforced the law collaborating with the company it regulated to build the compliance mechanism.
Three days later, on March 28, Apple removed four VPN and proxy apps from Russia's App Store at the request of Roskomnadzor, Russia's internet regulator. The apps, Streisand, V2Box, v2RayTun, and Happ Proxy Utility, were specifically built for circumventing Russia's deep packet inspection censorship infrastructure. Apple notified developers privately that their apps were removed because they "contain content that is illegal in Russia," and kept the removal private. Pavel Durov posted on X that the banned apps "helped users bypass Russia's DPI-based censorship" and put "users' online safety at risk."
Ok so let's reset on the Russia side for a second, because this week's removal is part of a much longer pattern. Apple pulled its first major wave of VPN apps from Russia's App Store in July 2024, 25 apps at once, including NordVPN, Proton VPN, and PIA. More waves followed through August and September 2024. By September 16, 2024, AppleCensorship.com's monitoring found 98 VPN apps unavailable in Russia's App Store, nearly four times the 25 that were officially reported. Add March 2026's removal of at least four more confirmed proxy tools and the historical total exceeds 100 apps, all removed without any Apple press conference, official acknowledgment, or public statement. Red Shield VPN, one of the July 2024 removals, published the letter they received and said: "Over the past six years, Russian authorities have blocked thousands of Red Shield VPN nodes but have been unable to prevent Russian users from accessing them. Apple, however, has done this job much more effectively."
Six years of state-level Roskomnadzor blocking barely dented VPN usage in Russia. One request to Apple made it happen instantly, for every iOS user who hadn't already downloaded the app.
The UK and Russia stories sound different on the surface, one is a censorship compliance story and the other is a children's safety story, but architecturally they're identical. Both times, a government made a demand and Apple complied, and users found out after the fact, if they found out at all, without a vote, an appeal process, or a public announcement. The same company that markets itself with privacy billboards at surveillance conferences will, when a government calls, make the change and move on. A centralized trust model means trust flows to regulators, and the users get whatever's left over.
The Biometric Update framed the UK verification shift correctly: Apple moved age verification from the app level to the account level, meaning it's now centralized. One decision at Apple affects identity enforcement across every service tied to that account. "If a single, non-transparent source defines the verdict, its errors propagate across all relying systems." The February 2026 accidental early activation in iOS 26.4 Beta 2 already demonstrated this: Apple's systems briefly triggered age verification on accounts that hadn't opted into the beta behavior, affecting users who had no idea why.
GrapheneOS is built on the opposite assumption.
GrapheneOS is an open-source Android build maintained by a small team, currently at release 2026032000 from March 20, 2026. It runs on Google Pixel hardware and, as of a Motorola partnership announced March 2, 2026, will expand to Motorola flagship devices in 2027. The OS excludes Google services entirely, and if you want Google Play, it runs as a sandboxed app inside a container with no system privileges, which means it can't reach the OS and has no special access to anything. Privacy Guides calls it "the best choice when it comes to privacy and security."
On an iPhone, your device's security depends on trusting Apple's closed codebase and trusting Apple's business decisions when a government calls. On GrapheneOS, the code is public, meaning anyone can read it, compile it, and verify it. Device integrity gets verified through hardware-backed attestation via the Auditor app, a cryptographic process independent of any company's servers or goodwill. The hardened memory allocator, JIT compilation restrictions, sandboxed apps, and hardware memory tagging on Pixel 8 and newer hardware are all documented and auditable. GrapheneOS lacks an app store for anyone to pull VPNs from and has zero account infrastructure to attach a government ID requirement to.
The architecture eliminates the compliance vector through design: companies can be pressured and requests can be processed, and open code running without a central authority removes both attack surfaces.
From what I've found, the people most surprised by this week's Apple news were iPhone users who had assumed that a company with privacy in its marketing materials would prioritize privacy over regulatory compliance. The assumption was always going to be wrong, because the architecture requires trusting Apple to make that call correctly in every jurisdiction, for every government request, forever. One bad call erases the track record, and this week there were two.
GrapheneOS shipped a security update on March 5, 2026 that patched an upstream Android vulnerability in Network permission enforcement for MediaPlayerService, and the fix arrived before Google's downstream release caught up. No government told them to and no compliance department reviewed it. The code was broken and users needed it fixed, and that was reason enough.